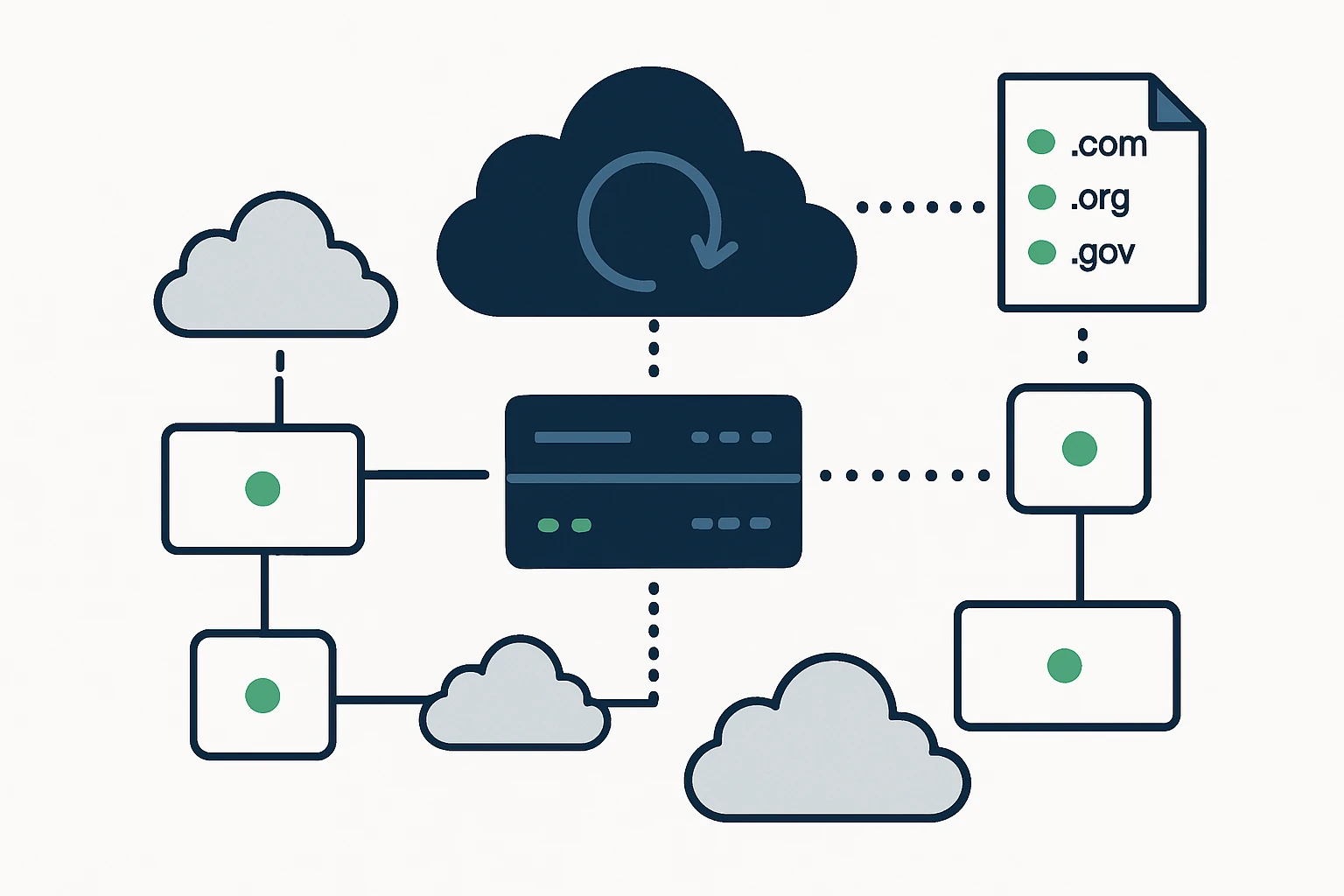
In modern multi-cloud environments, routing decisions are not only about where workloads live, but how end users reach them with low latency and high availability. DNS failover, traffic engineering, and the strategic use of domain assets by top-level domains (TLDs) can help teams steer traffic more intelligently. For organizations pursuing reliable, region-aware delivery, access to up-to-date domain lists by TLD can be a practical lever to improve decision-making. For example, resources such as download list of .ua domains and the broader List of domains by TLD page offer structured starting points for asset inventories that inform routing and failover planning.
Why Domain Lists by TLD Matter for DNS Failover and Traffic Steering
DNS-based failover relies on timely visibility into which endpoints are healthy and which should receive traffic. Domain lists by TLD contribute to this visibility in several concrete ways. First, they help security and risk teams model exposure across global namespaces, second, they support governance by clarifying ownership and hosting patterns at scale, and third, they enable more granular, data-driven routing decisions in multi-cloud networks. However, data quality matters: stale or improperly licensed lists can lead to misrouted traffic or compliance gaps. Cloud providers and DNS operators increasingly emphasize the need for reliable data and robust failover design to avoid noisy health checks or unintended outages. See Cloudflare’s DNS best-practices and failure-pitfalls guidance for related considerations. Cloudflare Whitepaper: Securing DNS - Pitfalls to Avoid.
Beyond data quality, the act of sourcing domain lists intersects with operational concerns like licensing, update cadence, and data provenance. As teams design failover and routing policies, they should pair domain-list data with authoritative DNS and health-check processes to ensure decisions reflect current infrastructure status.
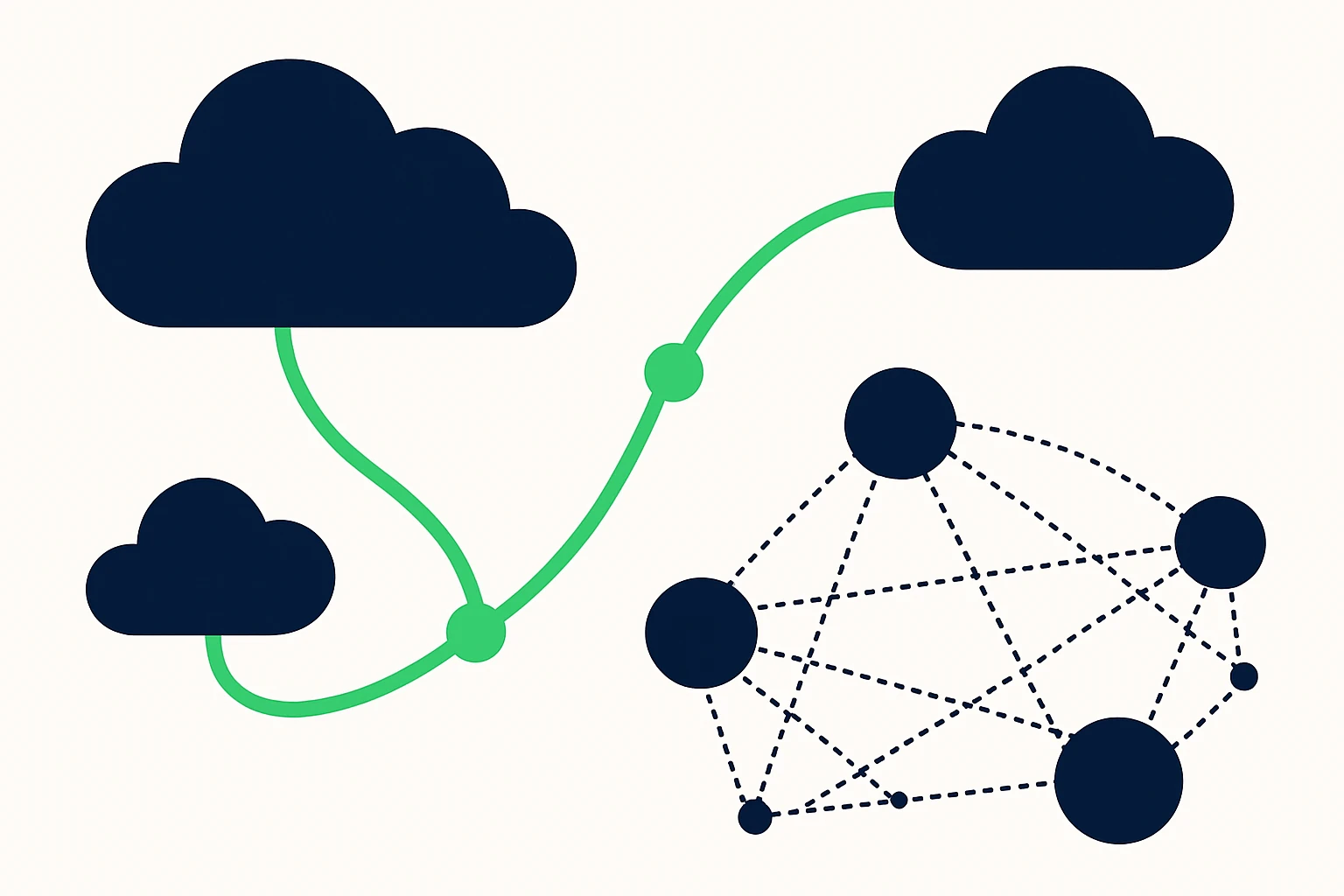
How Global Routing Works: Anycast and BGP Shaping
To translate domain lists into resilient traffic patterns, organizations frequently leverage global routing techniques such as IP anycast and Border Gateway Protocol (BGP) optimization. Anycast routing lets multiple geographically dispersed endpoints share a single IP address, allowing client requests to reach the nearest healthy instance and reducing perceived latency. This approach is a cornerstone of many CDNs and large-scale services that need to minimize distance and time-to-first-byte for users. ThousandEyes: What is Anycast IP addressing? describes how this paradigm works in practice and why it matters for global delivery. For a broader technical context, see overview material on Multiprotocol BGP and inter-domain routing strategies. Multiprotocol BGP provides foundational context on how BGP can carry multiple protocol families across diverse networks.
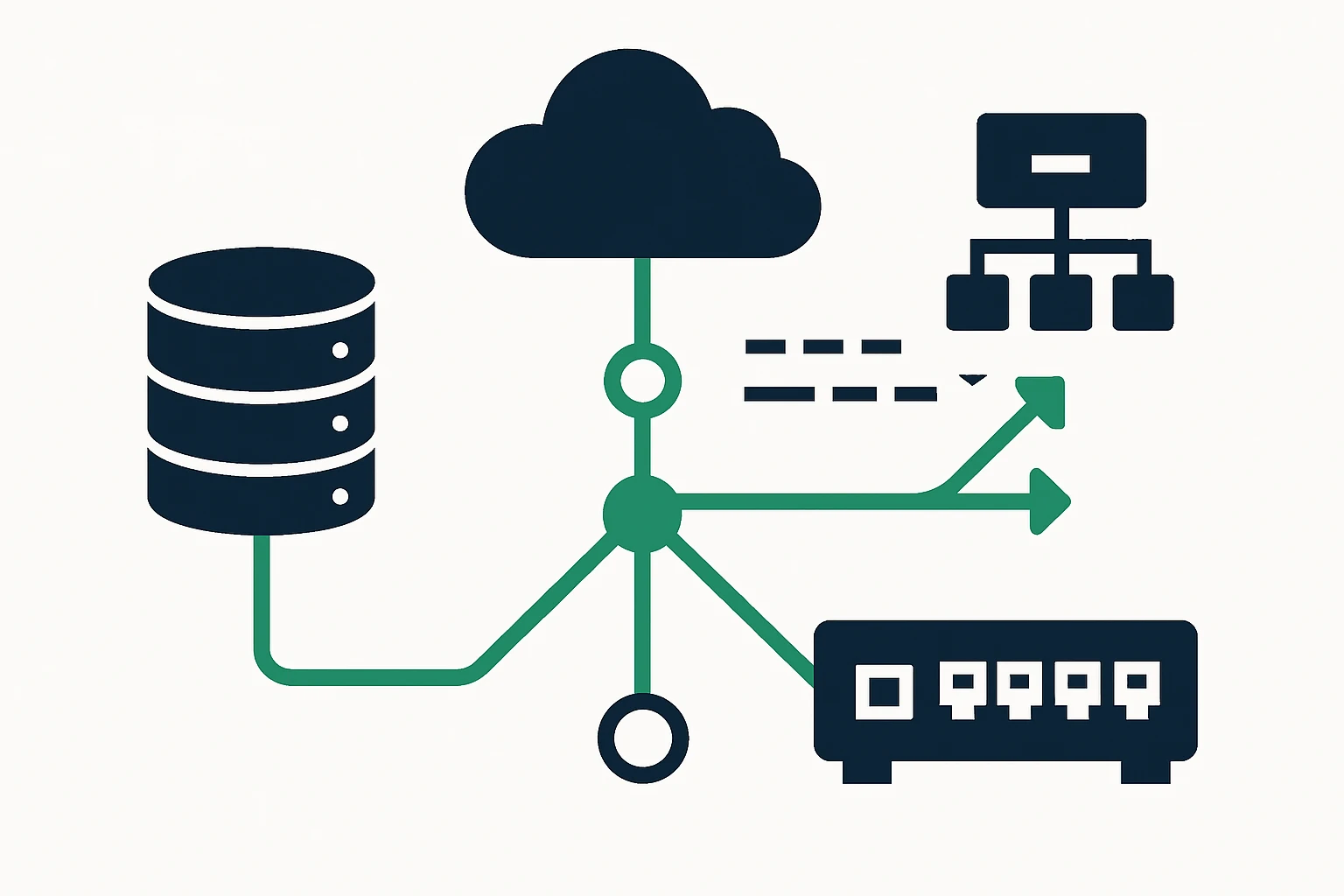
In parallel, traffic engineering continues to evolve with more sophisticated control planes that tune routes according to latency, bandwidth, and policy constraints. Industry resources detail these concepts and their practical implications for cross-cloud connectivity. For example, Cisco’s traffic-engineering guidance and related research illustrate how inter-domain and intra-domain routing can be optimized to support high-availability, low-latency paths in hybrid environments. Cisco: Traffic Engineering with Segment Routing and general multi-cloud best-practice literature offer actionable patterns for enterprises navigating complex topologies. NTT: 10 Great Practices to Manage Your Multicloud Environment.
A Practical Framework: Turning Domain Lists into Actionable Routing Decisions
The path from raw domain-list data to concrete routing behavior can be summarized in a four-step framework. It helps teams move from data collection to deployable, observable routing policies across cloud environments.
- Step 1 - Validate data quality and licensing. Assess the freshness, completeness, and licensing terms of domain-list data. Prioritize sources with clear provenance and API access for automated updates. For primary TLD assets, reference pages such as UA domain list and List of domains by TLD to anchor governance and risk assessments.
- Step 2 - Align DNS failover policies and TTLs. Define how quickly you want failover to react to health signals and consider how TTL settings interact with resolver caches. Contemporary DNS-failover guidance emphasizes the balance between responsiveness and stability, including the use of weighted endpoints and health checks. See Cloudflare’s adaptive routing and DNS-failover concepts for practical guidance. Adaptive routing basics and Round-robin DNS and zero-downtime failover concepts.
- Step 3 - Map data to routing strategies (anycast vs. BGP). Decide whether to deploy anycast for global latency reduction or to rely on BGP-driven traffic engineering to steer flows across providers. For a deeper dive into anycast benefits and limitations, see ThousandEyes: What is Anycast IP addressing?, and for BGP-oriented design, refer to Multiprotocol BGP.
- Step 4 - Establish observability and continuous improvement. Implement end-to-end monitoring, health checks, and change-control processes to validate routing decisions in production. Cisco’s practical guidance on hybrid-cloud networking underscored the importance of ongoing measurement and adjustment. Cisco: Segment Routing for TE and NTT: Multicloud best practices.
Structured quick-reference: a four-item framework
Data-to-decision mapping can be summarized as follows:
- Source data quality and licensing - ensure current, licensed TLD-domain lists.
- Policy alignment - translate data into TTLs, health checks, and routing rules.
- Routing strategy selection - decide between anycast for latency or BGP-based control for policy-driven paths.
- Operational visibility - instrument health, latency, and failover outcomes, with rapid feedback loops.
Limitations and common mistakes to avoid
Although domain-list data can sharpen DNS failover and routing decisions, several limitations and mistakes commonly appear in practice. First, data staleness is a persistent risk: lists must be updated at a cadence that matches your failover velocity. Cloudflare’s DNS guidance highlights the importance of planning for data freshness and failover reliability to avoid unintended outages. DNS pitfalls whitepaper.
Second, aggressive TTLs can backfire if resolvers aggressively cache old results, delaying failover or causing cache-stale traffic steering. Align TTLs with your health-check cadence and use server-side health signals to minimize risk. Practical guidance and real-world patterns are described in DNS failover and global load-balancing literature. DNS Failover best practices.
Finally, be mindful of overreliance on a single data source for critical routing decisions. Diversify sources, validate through independent probes, and keep a plan for manual failover if automated systems encounter edge-case failures. The broader literature on DNS resilience and edge routing emphasizes diversification and layered redundancy as core tenets. DNS resilience considerations.
Putting it all together: practical takeaways for cloud routing and traffic engineering
When you combine domain-list data with modern routing engines, you gain a data-informed view of how traffic can be steered across cloud providers, edge locations, and regional endpoints. The most effective implementations treat domain lists as a governance and decision-support layer rather than a single source of truth for live routing. They integrate domain-data sources with authoritative DNS, health checks, and global routing controls to achieve coordinated, resilient outcomes across AWS, GCP, and Azure networking setups. This approach aligns with best practices in multi-cloud networking and traffic engineering, while remaining adaptable to evolving network topologies and policy requirements.
In this landscape, CloudRoute offers a platform-friendly perspective on cloud routing and traffic engineering, including strategies that align with a domain-list-informed approach. While not the only path, such an integration can complement a broader toolkit that includes anything from global DNS load balancing to edge routing optimizations across providers.
Conclusion
Domain-list data by TLD can be a valuable, pragmatic input for DNS failover and multi-cloud traffic engineering, provided it is sourced responsibly, kept current, and paired with robust health checks and observability. By translating this data into disciplined routing policies and continuous validation, teams can reduce latency, improve uptime, and maintain governance across diverse cloud environments. As the cloud landscape evolves, a disciplined, data-informed approach to routing remains a cornerstone of resilient, high-performing applications.