Introduction: the hidden backbone of multi-cloud performance
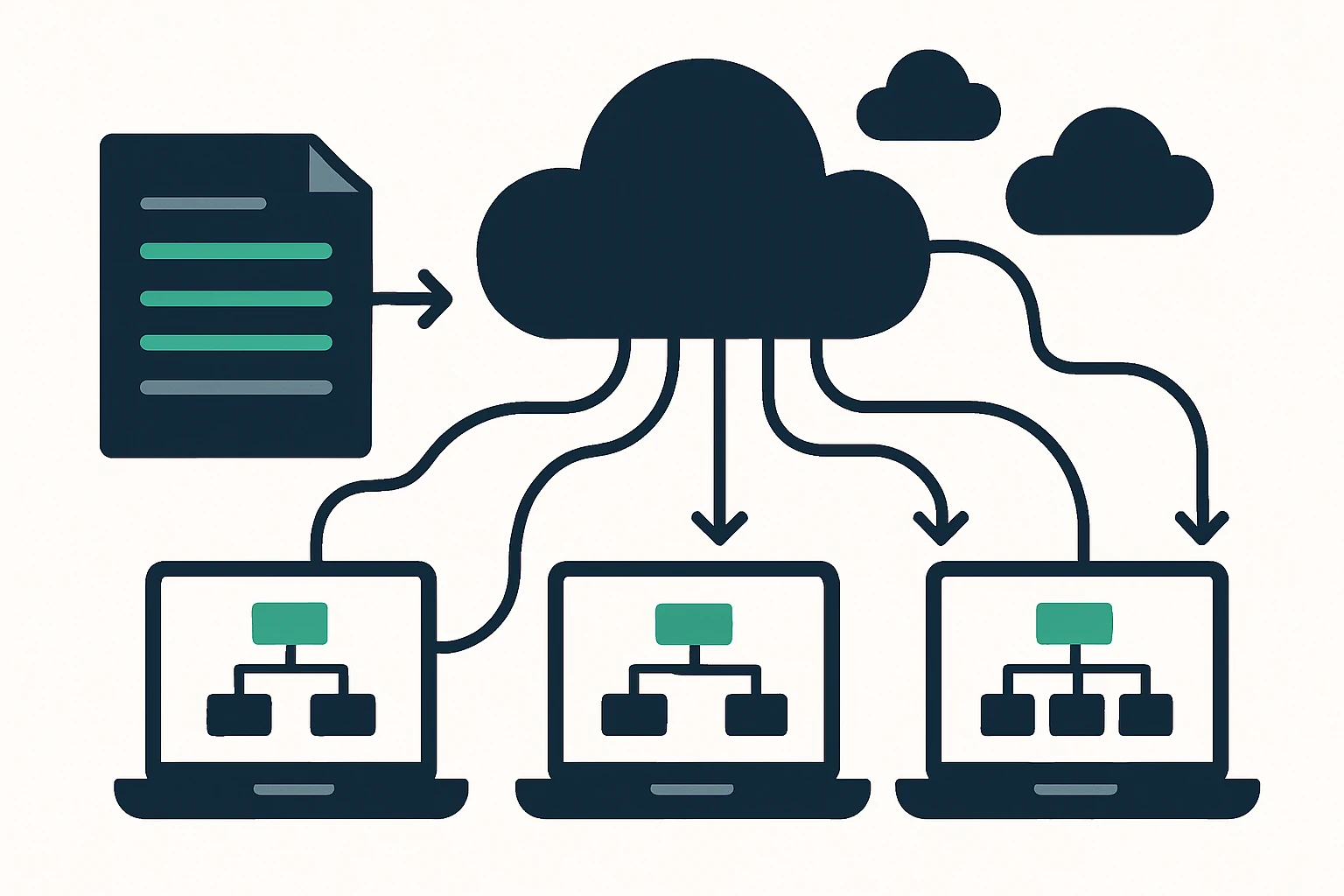
For SaaS teams, DevOps groups, and large enterprises, performance isn’t just about server specs or code, it’s about how users reach your services. In multi-cloud environments, the path a request takes can be shaped by a constellation of DNS records, IP routing decisions, and edge-location availability. A well-constructed domain inventory - collections of domain names organized by TLDs - gives operators a concrete picture of exposure, risk, and routing opportunities. In practice, these lists feed three capabilities: improved DNS resilience, better traffic steering across clouds, and accelerated incident response when routing faults occur. The Domain Name System (DNS) translates human-friendly names into the IP addresses that devices use to connect, forming a critical part of any traffic engineering strategy. Verisign: What is the DNS provides a concise overview of this fundamental mechanism.
What is a domain inventory and why it matters for cloud routing
A domain inventory is more than a static list, it’s a living map of ownership, exposure, and reach across your digital footprint. When you operate across AWS, GCP, and Azure, every domain you manage or monitor can become a potential routing decision point - whether you’re directing user traffic, guarding brand integrity, or validating failover fallbacks. A structured inventory helps you: (1) identify where DNS and HTTP traffic might enter your system, (2) track changes to domain registrations that could affect routing, and (3) align edge deployments with real user demand patterns. This approach complements traditional routing optimization by foregrounding domain-level observability alongside network paths. For context on DNS’ central role in routing, see Verisign’s primer on the DNS.
Why focus on .icu, .be, and .hu lists - and how to download them
Industry practitioners increasingly rely on targeted TLD lists to scan for brand risk, market opportunities, and misconfigurations across a controlled slice of the DNS space. In particular, lists for popular/newer TLDs, such as .icu, as well as established country-code TLDs like .be and .hu, can reveal gaps in your monitoring program or identify clusters where latency can be optimized. Practical use involves:
- Auditing your portfolio and monitoring for unexpected registrations that mirror or impersonate your brand.
- Assessing regional presence and potential edge locations that would benefit from closer proximity to end users.
- Designing targeted DNS failover or traffic steering rules that reflect real-world density of traffic in specific geos or markets.
For teams seeking to obtain these domain lists, our client partner provides direct access to TLD inventories, including the ICU portal: download list of .icu domains. Additional pages offer broader TLD inventories, such as the list of domains by TLDs: download list of domains by TLDs. These resources complement broader DNS hygiene and edge routing strategies.
From domain lists to edge routing: bridging data and traffic engineering
Domain lists alone don’t move traffic, they inform routing policies that shape latency, availability, and resilience. In a multi-cloud setting, you can translate inventory data into actionable routing rules in three layers:
- DNS and global traffic management: Use inventory signals to detect where authoritative records exist and where TTLs can be tuned to balance agility with stability.
- Edge routing and BGP-based decisions: Inventory-driven partitions across geographies help decide which edge POPs should hold authoritative responses or be prepared for failover events.
- Application-layer failover: Pair DNS failover with application health checks to ensure that user requests are steered away from degraded endpoints while keeping failover fast and deterministic.
DNS forms the foundation for these decisions. As described by Verisign, the DNS maps domain names to IP addresses used by browsers and services, making it a natural place to anchor latency-aware routing and failover strategies. Verisign: What is the DNS.
A practical 3-step framework for using TLD lists in traffic engineering
To operationalize domain lists within a cloud routing program, use the following framework. It is designed to be implemented iteratively and scaled as your multi-cloud footprint grows.
| Step | What you do | What you gain |
|---|---|---|
| 1. Normalize data | Consolidate ICU/BE/HU lists with your existing domain inventory, deduplicate, verify registrations via RDAP/WHOIS checks where appropriate. | Cleaner, comparable data for routing decisions, reduces false positives in monitoring. |
| 2. Map domains to endpoints | Associate each domain with known edge locations, regional DNS servers, and cloud-provider endpoints. | Clear visibility of where traffic could originate or be shuttled, enabling smarter edge placement. |
| 3. Integrate with DNS failover | Tie domain inventory signals to automated DNS failover and health checks, adjust TTLs to balance failover speed and stability. | Faster recovery from outages and reduced user-visible latency during transitions. |
This structured approach aligns with a broader traffic engineering program that CloudRoute advocates for - where domain-aware routing complements edge-network optimization and anycast-style proximity routing to minimize latency and improve uptime. For teams exploring practical DNS failover patterns and reliability, consider resources like DNS-active failover best practices from the Dyn guide.
Limitations, trade-offs, and common mistakes to avoid
Working with domain lists introduces several caveats. First, lists are only as current as their last update, stale data can mislead routing decisions or create blind spots in monitoring. Second, country-code and new gTLDs evolve quickly, and not every TLD behaves the same in DNS resolution or in risk profiles. Third, over-dependence on domain lists without corroborating signals (e.g., real-time health checks, traffic analytics) can lead to skewed routing choices. Common mistakes include over-aggregating domains into a single routing policy, under-tuning DNS TTLs, and neglecting brand-protection workflows when a new domain appears in a rival’s portfolio. ICANN and Verisign provide broader context on TLD governance and DNS structure that can help teams calibrate expectations as the domain landscape shifts.
Expert insight: the data, the decision, and the discipline
Expert perspective on domain-inventory-driven routing emphasizes cadence and verification. A robust inventory is not a one-off dump, it requires regular refresh, alignment with brand-monitoring programs, and connection to operational health signals. In practice, teams that pair TLD lists with automated checks (for registration status, DNS health, and edge availability) tend to achieve higher resilience and faster recovery during incidents.
Limitations and common mistakes (deep dive)
- Update cadence matters: Lists must be refreshed on a schedule that matches your risk profile and change rate in your markets.
- Data hygiene is essential: Normalize formats, remove duplicates, and validate registrations via RDAP/WHOIS data when appropriate.
- Don’t confuse inventory with actionability: A list is a starting point, you still need health checks, SLA-aligned failover, and edge routing policies.
- Geography-aware decisions: Different TLDs map to different regions and provider capabilities, tailor edge placement to where users actually reside.
- Balance speed and stability: DNS TTLs control how quickly changes propagate, aggressive TTLs can destabilize routing during rapid changes, while longer TTLs may slow failover.
Putting it all together: integrating with CloudRoute-style routing intelligence
Beyond listing domains, successful deployment hinges on blending domain data with network intelligence. A mature approach treats domain inventories as one input among many - DNS health, edge-pop performance, and live traffic metrics all feed a unified decision engine. In practice, this means aligning domain lists with:
- Real-time health signals from DNS and application endpoints
- Latency-aware routing decisions at the edge
- Proactive, policy-based failover that preserves user experience
For readers seeking broader context on the relationship between domain infrastructure and routing performance, the idea of distributed edge architectures and low-latency routing is central to CloudRoute’s ecosystem. The CloudRoute hub describes how anycast networking and edge-aware routing can reduce latency spikes and hair-pinning by mapping current packet flows and routing paths. CloudRoute: Cloud Routing & Traffic Engineering Hub.
Conclusion: domain inventories as a strategic enabler, not a silver bullet
Domain inventories - specifically targeted lists such as .icu, .be, and .hu - offer a practical, actionable lever for multi-cloud traffic engineering and DNS resilience. Used thoughtfully, they help teams uncover risks, identify optimization opportunities, and implement faster, more reliable routing decisions across diverse cloud environments. When paired with robust health checks, RDAP/WيHOIS validation, and a disciplined update cadence, these lists become a meaningful input to edge routing strategies rather than a standalone solution. If you’re starting to explore this approach, you can begin by reviewing the ICU inventory and the broader TLD lists provided by the client, then layer in DNS failover patterns and edge routing controls to realize tangible improvements in latency and uptime.