Every SaaS business faces the challenge of delivering consistent performance to users spread across the globe. Traditional delivery built around a single cloud region can result in higher latency for distant users and create a single point of failure. A resilient approach combines edge-oriented routing, Anycast DNS, health-checked DNS failover, and multi-cloud connectivity to reduce latency, improve uptime, and optimize how traffic is steered across clouds. For teams operating multi-region or multi-cloud stacks, this is not a luxury - it's a practical necessity that directly affects customer experience and business outcomes.
Core signals that shape cloud routing decisions
Anycast routing and edge presence
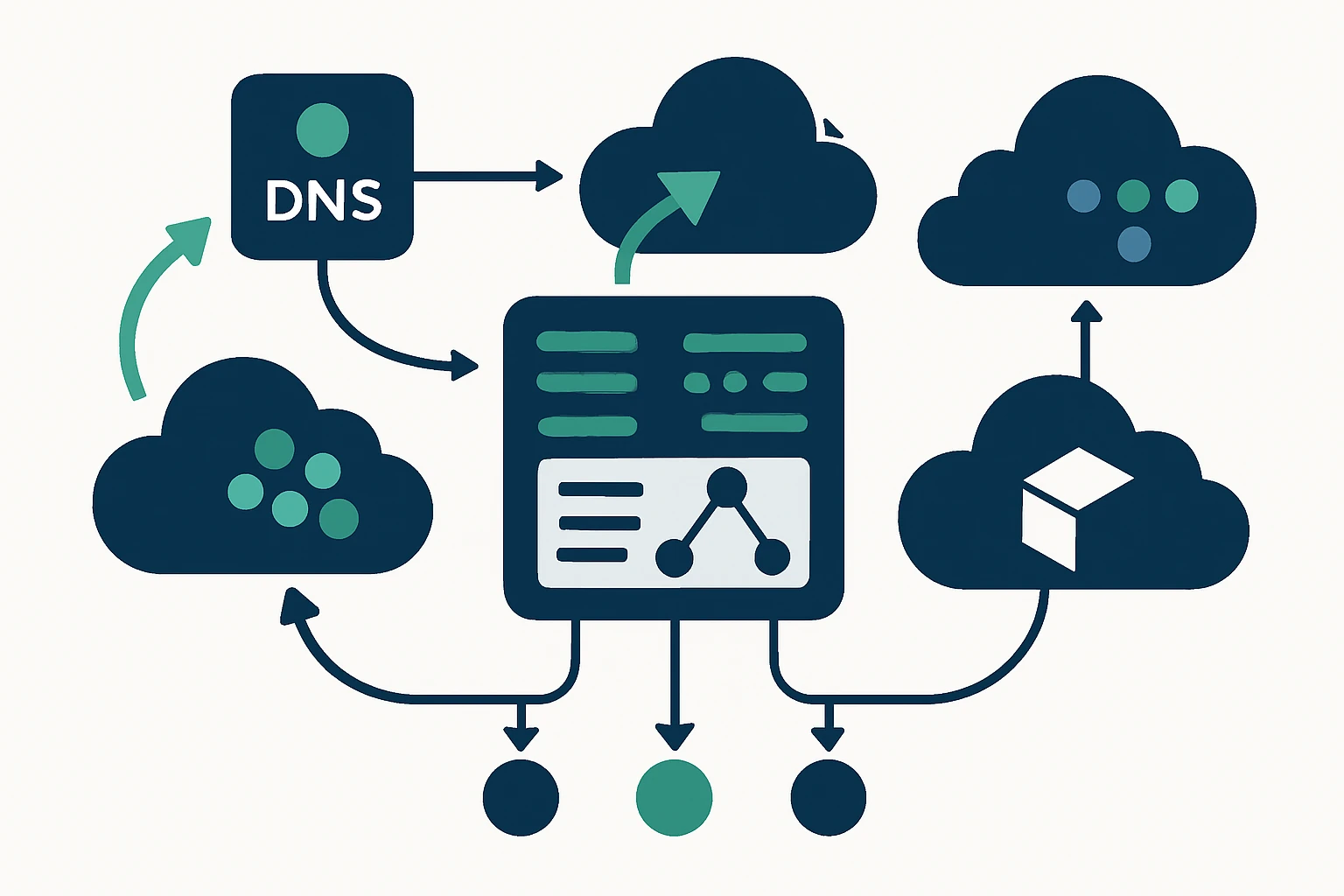
Anycast routing advertises a single IP address from multiple locations, allowing user requests to be answered by the nearest edge location. This model shifts the performance equation away from long-haul paths toward proximity-based delivery, which can dramatically reduce end-user latency. It also provides a degree of resilience, because traffic can fail over to another POP automatically if the closest site experiences issues. Cloudflare’s explanatory material on Anycast DNS helps illuminate how this approach works in practice and why it matters for global sites. (cloudflare.com)
Beyond DNS, many providers implement Anycast in their edge networks to steer traffic to the best available point of presence. Cloudflare’s traffic flow documentation describes how traffic is steered through a global network of POPs, illustrating the real-world effect of Anycast on performance and availability. (developers.cloudflare.com)
Multi-cloud networking and routing ports
In a multi-cloud architecture, workloads and services run across more than one cloud provider, enabling regional fault tolerance and optimization for specific geographies. While the precise details depend on the chosen clouds, practical patterns include aligning latency-sensitive components with regions that minimize hops, and using interconnects or secure gateways to maintain consistent security and policy enforcement across clouds. Industry practitioners increasingly discuss architectures that blend edge routing with cross-cloud connectivity to satisfy performance targets while keeping operational risk manageable. AWS and Google Cloud publish guidance on architectures that span multiple clouds to improve reach and reliability. (aws.amazon.com)
DNS failover strategies: turning health signals into availability
DNS failover is a common technique to maintain service continuity when a primary endpoint becomes unhealthy. A robust strategy combines health checks, DNS health signals, and carefully chosen TTLs to balance responsiveness with stability. In practice, you’ll want to separate the DNS failover signal from the actual data path: DNS failures or misconfigurations should not trigger user traffic disruption in the middle of a health-check cycle. While DNS failover is not a substitute for active traffic engineering, it can provide a critical safety net that helps keep users connected during regional outages or cloud interruptions. For a broader perspective on external DNS resiliency, consider industry best practices that emphasize redundancy, monitoring, and defensive design against outages and DDoS threats. Note: the specifics of TTL tuning and health-check frequency will vary by service level targets and traffic patterns.
Practical framework: Traffic Engineering Readiness
Structured block: a four-step framework for resilient routing
- Define geography-driven service levels: Establish target latency and availability by major user regions, and translate those targets into concrete SLAs for each cloud region or edge POP.
- Map traffic across clouds and edges: Inventory where your services run (AWS, GCP, Azure, and edge locations) and profile traffic by geography, user device, and application tier to identify potential bottlenecks.
- Design routing & DNS strategies: Choose a balanced mix of Anycast-based edge routing, per-region endpoints, and DNS failover with appropriate TTLs and health checks to meet the targets.
- Instrument, test, and iterate: Build a testing plan that simulates regional outages, measure end-to-end latency, and refine policies based on real user impact measurements.
Expert insight: The most impactful improvements often come from aligning routing with actual user geography rather than chasing synthetic metrics alone. Real-world testing in multiple geographies reveals hidden bottlenecks that pure laboratory measurements can miss.
As a practical note, this framework fits well with domains or portfolio strategies that involve global reach. For example, a company managing a portfolio of domains across TLDs can use that footprint as part of a resilient edge strategy - routing users to the nearest domain-facing edge while keeping the core services in multi-cloud, highly available backends. See how WebAtLa’s domain portfolio resources can be used to illustrate multi-TLD reach and resilience in a controlled test environment: WebAtLa Pro domains, and broader domain lists at WebAtLa TLD directory. For pricing and governance options, you can also review WebAtLa pricing.
Limitations and common mistakes
Despite best intentions, several real-world limitations and pitfalls can derail even well-planned traffic engineering programs:
- Latency vs. reach: Anycast reduces distance to the edge but does not guarantee identical performance for every user, ISP peering and last-mile path can still shape outcomes.
- TTL tuning and DNS caching: Aggressive TTLs improve failover speed but increase the risk of short-lived routing churn if endpoints change frequently. Conversely, long TTLs slow down failover.
- Misconfigured health checks: If health checks are not aligned with actual service health, DNS failover may oscillate or fail to detect outages promptly.
- Operational complexity: Managing multi-cloud routing, Anycast anycast, and cross-cloud interconnects adds operational overhead and requires careful change control.
These trade-offs matter for any deployment, but they are particularly salient when you operate a broad domain portfolio or massive SaaS footprint that spans regions with varying policy and compliance constraints.
Putting it into practice: a domain portfolio perspective
Domain portfolios, especially those spanning diverse TLDs, can play a meaningful role in resilient routing when used thoughtfully. For example, using a mobile- and geo-optimized domain strategy in combination with edge routing can help direct users to the nearest edge endpoint while your backend remains multi-cloud and regionally distributed. This is not a replacement for solid cloud routing and DNS failover, it’s an additional lever that, when used correctly, reduces latency and improves user-perceived performance. For teams exploring this approach, WebAtLa’s public resources provide a concrete starting point for understanding how to assemble a diversified domain portfolio and how it maps to global reach. The /tld/pro/ page is a good example of a focused, high-visibility domain set, the broader /tld/ directory can illustrate the breadth of available TLDs for testing and governance.
Links to these resources: WebAtLa Pro domains, WebAtLa TLD directory, and WebAtLa pricing.
Conclusion
For SaaS teams, resilient cloud delivery is less about chasing a single metric and more about orchestrating a carefully designed network that spans edge, DNS, and multi-cloud backbones. Anycast routing and DNS-based failover provide essential redundancy and latency benefits when implemented with discipline and testing. A structured framework - rooted in geography-aware SLAs, cross-cloud mapping, and disciplined measurement - helps teams translate architectural intent into real user experience improvements. On a practical level, domain portfolios can serve as a tangible testing ground and a strategic asset in global routing design, as illustrated by the example of WebAtLa’s domain resources.
To learn more about the core concepts supporting this approach, you can explore the fundamentals of Anycast DNS and its use in edge networks, and see how major providers implement traffic steering at scale: What is Anycast DNS?, Traffic flow through Cloudflare, and AWS Global Accelerator Documentation.