Introduction
For software-as-a-service (SaaS) products, performance and reliability are not afterthoughts - they are the core of product experience. As teams deploy across multiple cloud providers (AWS, Google Cloud, Azure) and edge locations, the plumbing that carries customer traffic becomes a strategic differentiator. DNS resolution, routing decisions, and even which top-level domains (TLDs) you own can influence latency, resiliency, and trust. In this article, we explore a domain-driven approach to traffic engineering that aligns with multi-cloud networking goals, explains how modern DNS and routing work together to reduce latency, and offers a practical framework you can apply today. The discussion draws on industry practices around anycast and DNS failover, and points to credible resources for teams that want to source domain datasets (including specialized lists like .io, .app, and .bond) to inform architecture and branding decisions.
What problem are we solving? When a SaaS service spans multiple clouds and geographies, users should reach the nearest healthy endpoint with minimal delay, and outages should be recoverable without perceptible disruption. Achieving this requires both robust traffic engineering and a domain strategy that supports fast, resilient redirection. As you read, you’ll see how domain lists and DNS-based routing can be part of a broader, architecture-first approach to cloud routing optimization and multi-cloud networking.
1) The essentials: how DNS, anycast, and multi-cloud networking interact
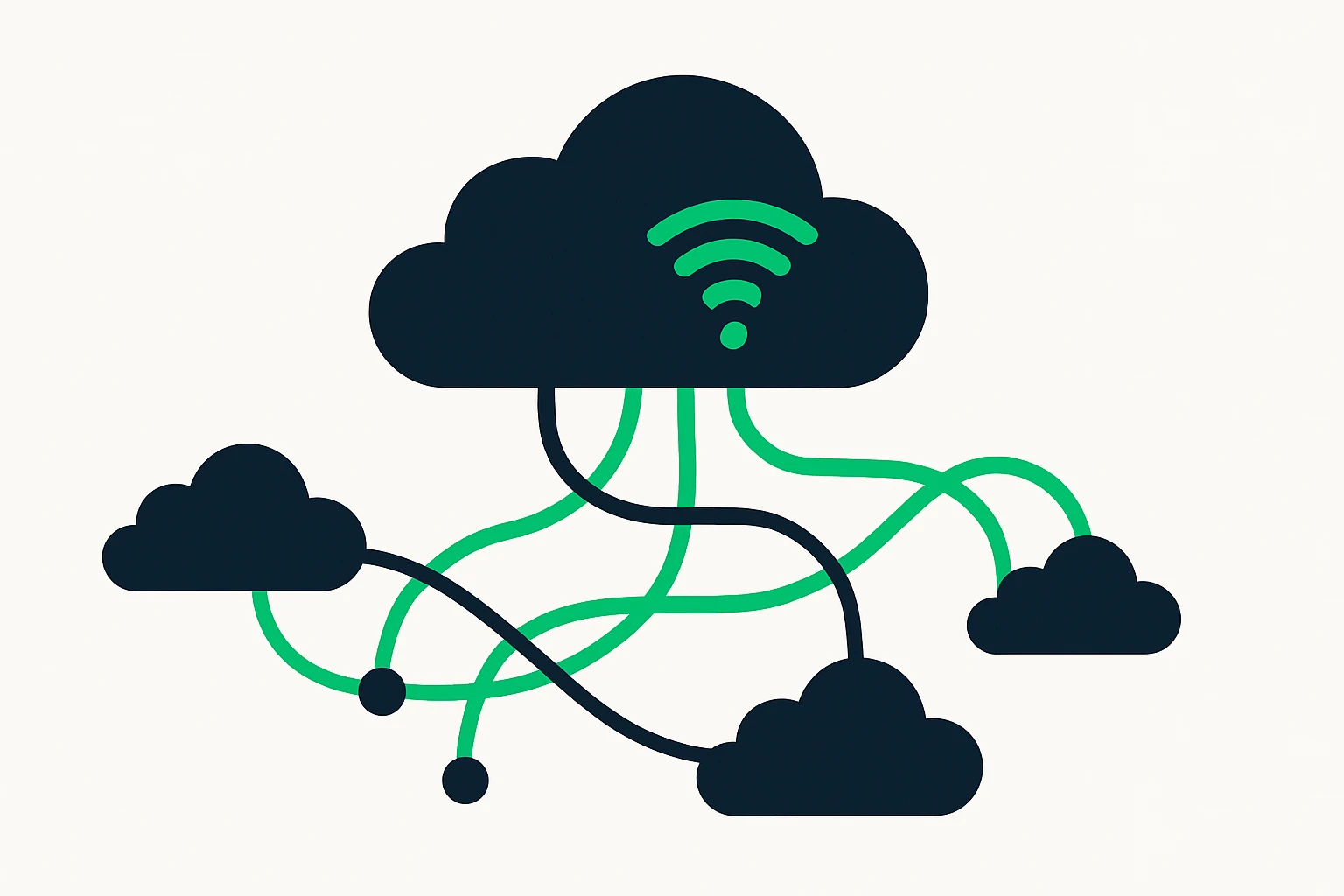
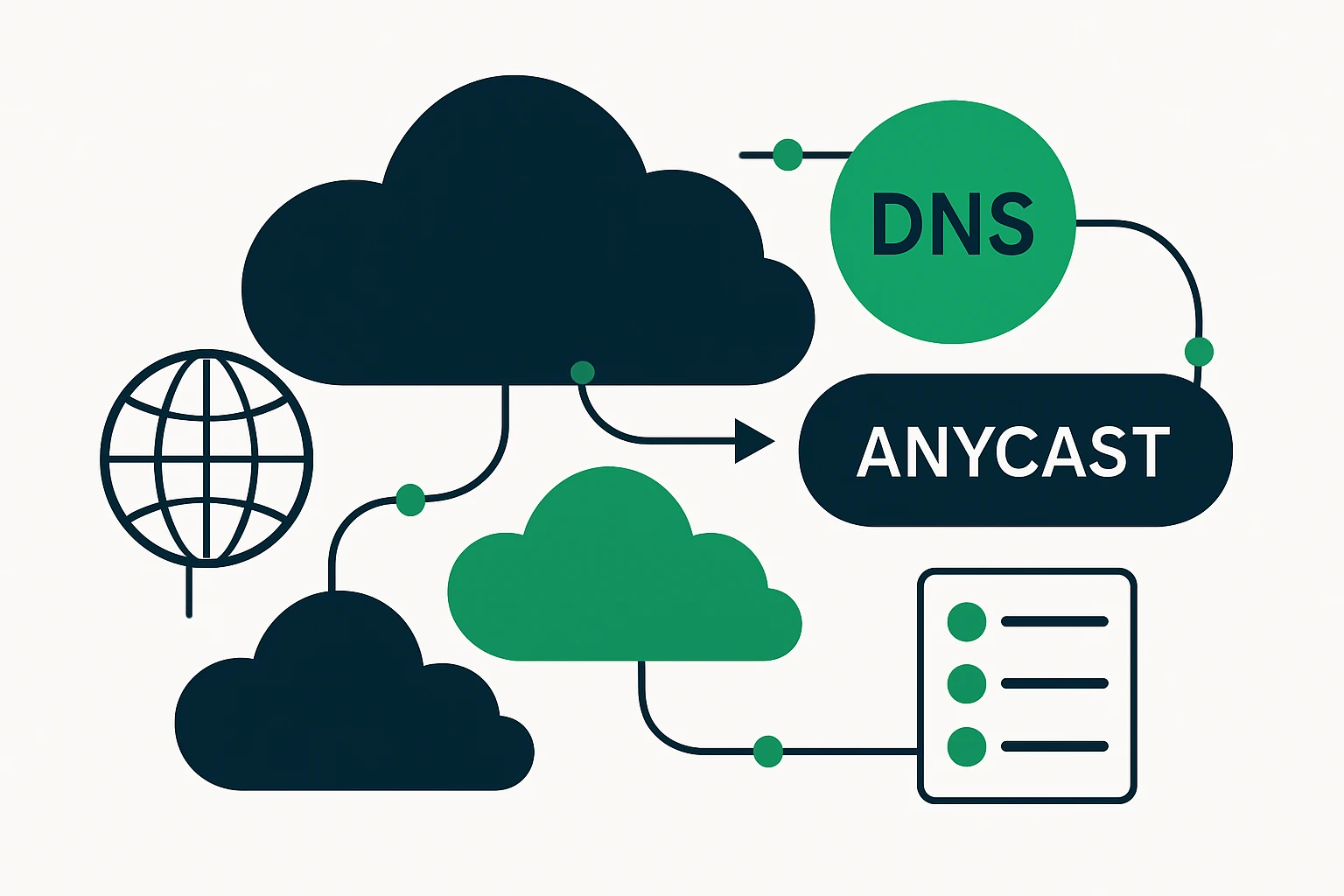
Two technologies sit at the heart of latency reduction and high availability in modern networks: anycast routing and DNS-based failover. Anycast allows the same IP address to be served by multiple, geographically dispersed endpoints. When a user resolves that IP, the network directs the query to the closest healthy instance, reducing round-trip times and improving failover latency. In practice, many DNS and CDN providers leverage anycast to route traffic to the nearest data center or edge node, which is a key part of a resilient, low-latency SaaS delivery chain. Cloudflare’s overview of Anycast DNS explains how multiple data centers can respond to the same DNS namespace, distributing load and increasing fault tolerance. (cloudflare.com)
Beyond raw latency, hybrid DNS routing - combining unicast and anycast strategies - can optimize availability and performance for large-scale deployments. Verisign’s announcement of a hybrid unicast/anycast approach illustrates how DNS providers blend routing methods to maximize uptime while preserving fast lookups. This dual-path approach is especially relevant when you operate across regions and clouds with varying network characteristics. Verisign: Hybrid Unicast and Anycast DNS. (investor.verisign.com)
For practitioners focused on reliability, DNS-based high-availability strategies are a proven pattern, but they come with caveats. DNS failover relies on health checks, monitoring, and sensible TTLs, it is most effective when used in tandem with application-layer health signals and load balancing. Cisco’s DNS HA guidance emphasizes planning, monitoring, and redundancy as part of a cohesive DNS strategy. Cisco: Managing High Availability DNS. (cisco.com)
2) A practical framework: domain strategy for resilient, multi-cloud SaaS
To translate the technology concepts above into practice, consider a three-stage framework that integrates domain data, DNS routing, and cloud topology decisions. This framework keeps a tight feedback loop between architecture and branding assets (domains and DNS) while staying aligned with cloud routing optimization and network performance priorities.
| Stage | Key Actions | Expected Outcomes |
|---|---|---|
| 1. Map the cloud footprint |
|
Clear map of where traffic originates and where it should be served from most efficiently. |
| 2. Design the domain and DNS strategy |
|
An architecture-neutral DNS strategy that supports rapid redirection with minimal user-perceived latency. |
| 3. Execute and monitor |
|
Operational visibility and the ability to tune routing rules as cloud performance evolves. |
Expert insight: In large-scale deployments, traffic shaping decisions should be informed by both network performance data and application-level health signals. An experienced DNS architect notes that TTLs should be conservative enough to allow rapid failover yet not so short that they create instability or DNS floods in edge networks. Pairing DNS failover with continuous health checks at the application layer is essential for reliable experience across cloud boundaries.
3) Limitations, trade-offs, and common mistakes
There is no silver bullet. DNS-based failover and anycast routing offer powerful levers, but they come with trade-offs and pitfalls that teams must manage directly.
- TTL and cache effects. DNS failover relies on TTL values, overly aggressive TTLs can lead to flapping and higher DNS load, while long TTLs slow down recovery after an outage. The right balance depends on your RTO targets and user base.
- DNS is not a guarantee of instant rerouting. Even with quick DNS responses, client resolvers and browsers may cache old IPs, causing delayed failover. Complement DNS-based strategies with regional load balancing and edge routing where possible.
- Reliance on a single DNS provider. Centralizing DNS during a multi-cloud rollout raises the risk of a single point of failure. Consider hybrid or multi-provider setups and trigger-driven failover that keeps control in your architecture.
- Geo-routing pitfalls. Geographical routing can misrepresent network conditions if not continuously calibrated, network conditions change, and stale routing often hurts more than it helps.
- Over-optimization for one metric. Chasing the lowest latency can lead to suboptimal routes or higher costs, every optimization has a trade-off in resilience, operational complexity, or brand strategy (see the section on domain lists).
These realities underscore why a structured, data-informed framework matters. DNS-based strategies work best when anchored to cloud topology, service-level objectives, and ongoing measurement - otherwise, you risk creating a brittle system that looks fast in theory but performs poorly under real outages.
4) A quick reality check on domain lists and TLD choices
As teams explore domain-backed strategies, specialized domain lists - such as those for .io, .app, and other modern TLDs - can play a role in branding, regional signaling, and even vendor associations. In practice, many tech startups view .io as a signal of developer focus and technical credibility, while other TLDs may support regional branding or specific product lines. Market intelligence and industry data show ongoing interest in non-.com domains among tech startups, though the relative value of any single TLD depends on your audience, branding, and trust considerations. For example, industry and market coverage note continued demand for .io and related tech-oriented TLDs, with broader shifts in domain strategy among startups. Forbes Tech Council: The Future of .IO Domains. (forbes.com)
In addition, credible market analyses highlight the resilience benefits of modern DNS architectures and anycast-driven delivery, which supports the argument for integrating domain decisions into traffic engineering. A recent overview explains how anycast DNS distributes queries to the nearest data center, contributing to lower latency and robust availability. Cloudflare: What is Anycast DNS?. (cloudflare.com)
5) Resources for obtaining domain datasets
For teams that want to operationalize this guidance, periodical access to domain datasets across TLDs can accelerate discovery and testing. The following client resources provide structured lists of domains by TLD and related data that teams may use for benchmarking, branding decisions, or inventory planning:
Beyond these options, consider expanding the data footprint to include regional and technology-focused categorizations to align with your cloud footprint and market strategy.
6) How to apply this in practice: a minimal, actionable playbook
To operationalize the framework without delaying velocity, practitioners can adopt the following practical playbook:
- Audit cloud regions and identify the top latency-sensitive user cohorts.
- Draft a domain strategy that supports branding, resilience, and regional signaling - consider io, app, and bond as part of the portfolio where appropriate.
- Implement DNS failover with measured TTLs and application-layer health checks, enable anycast routing for DNS/CDN endpoints if supported by your provider.
- Build dashboards that track DNS resolution time, failover events, and end-to-end latency from user to service across clouds.
- Iterate quarterly based on performance data and market trends in domain naming (e.g., growing interest in non-.com domains among tech startups).
As you expand, stay mindful of trade-offs between latency, resilience, cost, and brand policy. The end goal is a coherent system where domain data, DNS routing, and cloud topology mutually reinforce your performance and reliability targets.
Conclusion
In a multi-cloud SaaS landscape, traffic engineering is as much about the domain strategy as it is about network protocols. By combining an informed approach to DNS failover and anycast routing with deliberate choices about TLDs and domain datasets, engineering teams can shorten response times, reduce the blast radius of outages, and present a credible, brand-aligned digital identity to customers. The three-stage framework - map the cloud footprint, design the domain/DNS strategy, and execute with continuous monitoring - offers a practical path from concept to measurable improvements in cloud network performance. For teams looking to explore domain datasets and related resources, the links above provide concrete entry points to begin building a resilient, high-performance SaaS delivery model.