Introduction: A new angle on an old problem
For modern cloud operators, SaaS providers, and digital teams, the domain landscape is not just a peripheral concern. It shapes brand trust, protects customers from phishing, and informs decisions about global reach and latency. As new generic top-level domains (gTLDs) like .design, .cat, and .solutions proliferate, teams increasingly rely on downloadable domain lists to ground strategy in data. This article offers a practical approach to leveraging these lists for brand governance, threat detection, and cloud routing optimization - without turning this into a marketing checklist.
To set the stage: the DNS root maintains a formal record of every top-level domain and its operator. Among gTLDs, .design is classified as a generic TLD, not tied to a country, which has implications for branding and scope. This classification comes from the authoritative IANA Root Zone Database, which is the global reference for TLD delegation. (iana.org)
The domain landscape and why it matters for cloud strategy
In the past decade, the DNS has expanded far beyond .com and country-code TLDs. ICANN’s New gTLD Program opened the door to hundreds of new endings, enabling brands and organizations to express identity more precisely at the root of the internet. For architecture teams, this matters because domain choices can influence accessibility, brand integrity, and user trust across multi-cloud deployments. The program’s intent - and the ensuing market dynamics - are documented by ICANN as a governance framework that expands branding opportunities while requiring careful risk management. (newgtldprogram.icann.org)
From a practical standpoint, downloading and analyzing lists of specific TLDs - such as design-, cat-, and solutions-themed domains - gives teams a view into the evolving digital footprint of related ecosystems. It also supports proactive monitoring for brand impersonation, portfolio hygiene, and proactive risk assessments that feed into routing and traffic engineering decisions. However, the value depends on data quality, timely updates, and proper interpretation of edge cases in domain ownership and status. Industry observers also note that the SEO value of new gTLDs is nuanced and context-dependent, so lists should inform, not override, a broader branding and technical strategy. (dn.org)
For organizations evaluating such lists, WebAtla provides categorized domain directories by TLD, including design-specific groupings, to help teams assemble relevant datasets quickly. See the design TLD page and the broader TLD index as starting points for a structured data pull. WebAtla design TLD directory and WebAtla TLD index.
Use cases: what you can do with downloadable domain lists
Downloaded domain lists for .design, .cat, and .solutions can support several operational goals within cloud routing and traffic engineering contexts:
- Brand hygiene and risk monitoring: Identify potential typosquatting and brand impersonation by scanning for domain names that closely resemble your own brand across these extensions. This informs defensive registrations and alerting workflows within security operations and cloud edge routing rules.
- Market and regional strategy: Map where design- or solution-focused domains are registering or parking in different regions, which can guide multi-cloud distribution choices and latency-aware routing decisions across geographies.
- Supply-chain and vendor risk assessment: A structured view of who is registering design- or solution-oriented domains can expose partnerships, affiliates, and third-party risk vectors that affect DNS configurations and failover planning.
- Branding experiments and product naming: Use descriptive TLDs to evaluate naming concepts for pilots, a/b tests, or new product initiatives, while maintaining a consistent cloud- and network-architecture footprint.
These use cases are most effective when the data is treated as a starting point for qualitative analysis and governance processes, rather than as a final arbiter of brand strategy. The ability to download and programmatically refresh these lists accelerates both discovery and validation within cloud environments.
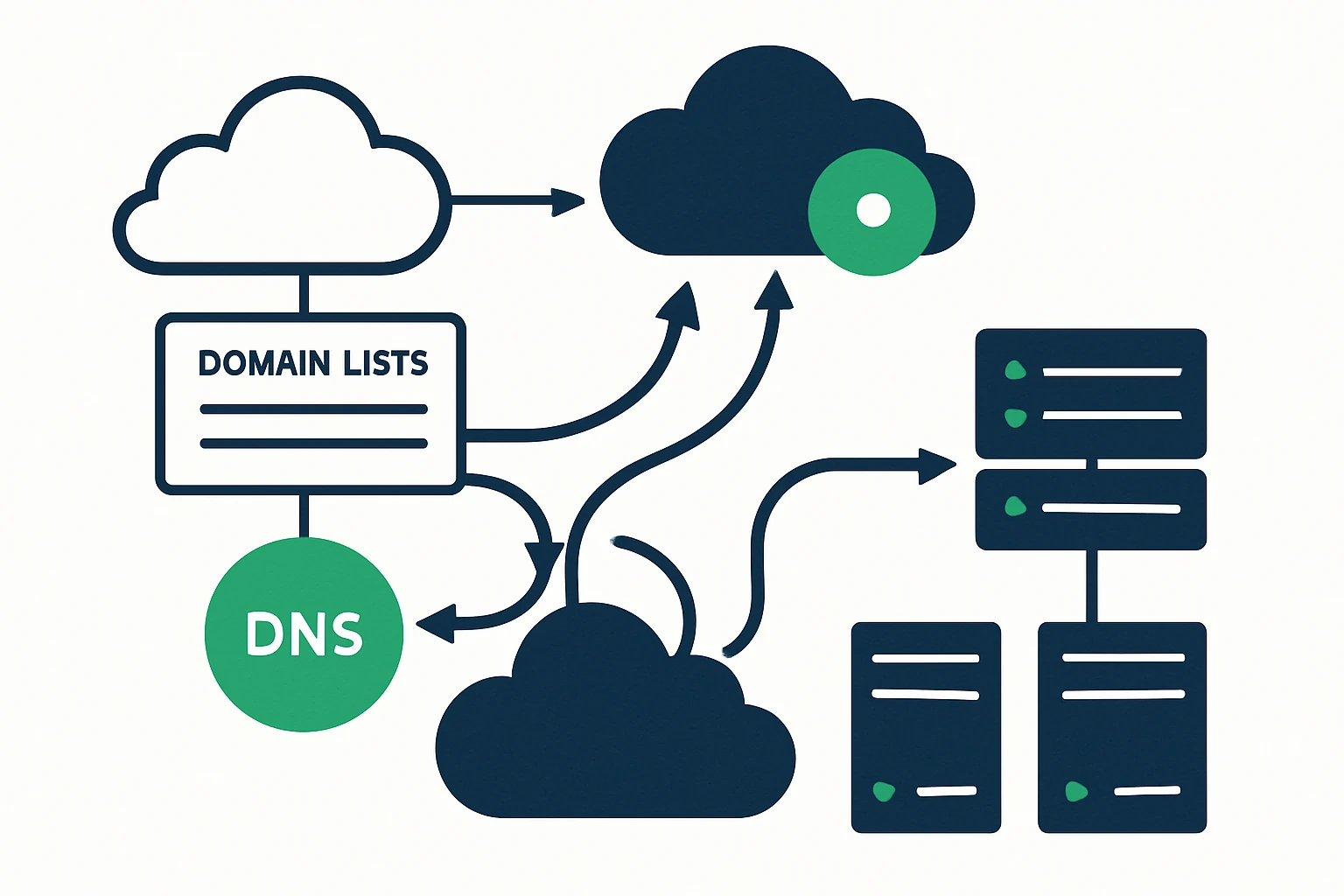
Framework: a three-step process to turn domain lists into action
To make domain lists actionable in a cloud routing and traffic engineering context, apply a lightweight, repeatable framework. The following three steps form a practical workflow that your team can adapt without overhauling existing processes.
- Discover - Define the scope and quality criteria. Determine which TLDs matter (for example, design, cat, solutions) and set thresholds for inclusion (e.g., active registrations vs. parked domains, regional distribution, or ownership patterns). This step also includes aligning on governance policies for data use and privacy compliance.
- Validate - Sanity-check the data. Confirm ownership and current status using reliable sources (RDAP/WHOIS data where available), filter out obvious noise (expired domains, typosquats far removed from the brand, or domains with minimal activity), and annotate edge cases (brand-name collisions, licensing issues, or regional restrictions). Validation protects you from acting on stale or misleading signals.
- Apply - Integrate the validated signals into cloud routing and brand governance. Use the list to inform edge-layer policies, DNS failover strategies, and monitoring rules that trigger alerts when new or suspicious domains appear in relevant namespaces. Treat the data as a feed into decision workflows rather than a standalone control plane.
Structured below is a compact framework you can reuse in planning meetings, vendor reviews, and security postures. This is not a rigid template, it is a pragmatic, auditable process aligned with how cloud networks operate today.
A practical, repeatable framework (three-step model)
- Step 1: Discover
- Identify target TLDs: .design, .cat, .solutions
- Clarify data needs: status, ownership, regional distribution
- Set governance boundaries: privacy, consent, and data retention
- Step 2: Validate
- Cross-check with RDAP/Whois data where available
- Filter parked/expired domains and obvious impersonations
- Annotate ambiguous cases for legal and security review
- Step 3: Apply
- Incorporate signals into DNS failover and routing rules
- Document decisions for change-control processes
- Review outcomes in regular governance rounds
Tip: Treat this as a living feed. As ICANN and the domain ecosystem evolve, your framework should adapt, and your data refresh cadence should reflect risk levels and business cycles. The New gTLD Program remains a governance framework that has expanded branding opportunities while requiring ongoing risk management. (newgtldprogram.icann.org)
Expert insight: how practitioners view new gTLDs today
Industry observers emphasize that new gTLDs can be powerful branding tools when paired with disciplined governance and technical controls. A thoughtful approach recognizes both opportunity and risk: new endings can convey identity and domain strategy clarity, but they also demand robust brand protection and DNS governance to prevent confusion or abuse. ICANN’s governance materials stress safeguards that help organizations balance brand opportunity with consumer protection and operational reliability. Expert insight: consider new gTLDs as extensions of your brand architecture, not as shortcuts for marketing alone. Use them to signal intent and expand reach, while embedding these signals into your DNS and security plans. (newgtldprogram.icann.org)
Limitations and common mistakes to avoid
While downloadable domain lists offer clear value, there are notable limitations and frequent missteps to watch for:
- Data freshness and quality: lists quickly go stale if not refreshed. Parked domains, expired registrations, and dynamic ownership can distort signals if not filtered carefully.
- SEO and branding myths: some teams assume that a new gTLD automatically improves search rankings or brand credibility. In practice, search algorithms treat TLDs as one of many signals, the branding, user experience, and content quality still dominate. This nuance is discussed in industry analyses of new gTLD adoption and SEO considerations. (dn.org)
- Over-reliance on lists for decision-making: domain lists should inform governance and risk management, not replace due diligence, legal reviews, or customer trust considerations.
- Governance gaps: without clear ownership, privacy, and retention policies, data-use practices can create compliance risk and slow operational response during incidents.
Incorporating authoritative safeguards - such as integrity checks, clear ownership validation, and routine governance reviews - helps teams avoid these pitfalls. ICANN’s safeguards and ongoing program materials emphasize that the benefits of new gTLDs come with an obligation to manage risk and protect consumers. (gac.icann.org)
Why it matters for CloudRoute readers
CloudRoute’s focus is on cloud routing optimization and traffic engineering. Domain lists don’t replace network design, but they can inform edge-selection strategies, failover readiness, and security monitoring in a multi-cloud environment. By understanding which design-, cat-, or solutions-themed domains are active, organizations can better map their traffic engineering policies to real-world brand and market dynamics. The resulting data-informed routing decisions can contribute to latency reduction, uptime improvements, and more predictable cloud network performance, complementing traditional routing metrics and BGP optimization efforts.
For teams ready to explore, WebAtla’s domain directories present a practical resource to begin a structured pull of relevant TLDs. See the design-specific directory and the broader TLD index to assemble a targeted dataset that supports your brand and network strategy. WebAtla design TLD directory • WebAtla TLD index.
Limitations, trade-offs, and common mistakes (summary)
- Brand opportunity vs. implementation cost: Brand signals in new gTLDs require legal, branding, and DNS infrastructure investment.
- Signal vs. noise: Not every domain in a list will be meaningful for your brand or routing policy, filtering is essential.
- Data stewardship: Regular refreshes and clear data-ownership rules are necessary to maintain trust and compliance.
Conclusion: a disciplined path to harnessing domain lists
Downloadable lists of .design, .cat, and .solutions domains offer a practical lens to understand brand ecosystems, security risks, and the opportunities afforded by the evolving DNS landscape. When integrated with a disciplined framework - Discover, Validate, Apply - such data becomes a productive input to brand governance and cloud routing decisions, not a marketing gimmick. By combining authoritative sources, careful data hygiene, and governance processes, teams can turn domain-list insights into tangible improvements in reliability, brand integrity, and global performance. For teams that want to go further, consider sourcing domain directories directly from trusted providers like WebAtla and incorporating them into your security and network operations workflows.
Recommended further reading and resources: WebAtla design TLD directory, WebAtla TLD index, and the IANA Root Zone Database for authoritative TLD classifications. (iana.org)