Introduction: why domain lists matter for cloud routing and traffic engineering
In complex cloud ecosystems - where organizations rely on multi-cloud deployments and global edge networks - knowing which external domains exist and how they behave can dramatically influence routing decisions. For teams building disaster recovery plans, optimizing latency, or protecting brands across regions, domain intelligence becomes a practical input for DNS failover, traffic steering, and edge routing strategies. A topic that often surfaces in technical conversations is how to download list of .cz domains, download list of .me domains, and download list of .at domains for inventory and testing. This article lays out a structured approach to obtaining and using these domain lists responsibly, with a view toward real-world cloud routing and traffic engineering needs.
Why domain lists are relevant to cloud routing and traffic engineering
Domain lists can inform several critical activities in modern networks:
- Inventory and risk assessment: A comprehensive view of external domains helps teams map potential attack surfaces, supply-chain dependencies, and service integrations that may influence routing choices.
- DNS failover and resilience: When paired with health checks and routing policies, domain data supports automated failover decisions and regional traffic distribution.
- Threat intel and brand protection: Keeping tabs on domain registrations and usage patterns aids in detecting spoofing, phishing, or misrepresentation that could affect user trust and application reach.
- Traffic engineering across clouds: In multi-cloud environments, understanding domain footprints helps design routing that respects latency, egress costs, and regional availability.
Industry guidance on DNS reliability and routing supports these practices. For example, modern DNS strategies often rely on failover policies and latency-based routing to reduce downtime and improve user experience, as described in practical AWS Route 53 guidance. Configuring DNS failover and general best practices emphasize latency-aware routing and health-based decision-making. Best practices for Route 53 provide a broader view of how to design resilient, scalable DNS-based routing.
The cz, me, and at domains: what they offer and where to obtain them
Three popular country-code TLDs often appear in enterprise data sets due to market presence and regional traffic patterns. The ability to download lists of domains within these TLDs can aid in regional testing, inventorying external endpoints, and validating DNS failover scenarios in a controlled manner.
- .cz domains (Czech Republic) can be useful for assessing regional edge endpoints and local DNS behavior.
- .me domains (Montenegro-country code delegated as a domain in multiple contexts) frequently appear in consumer-facing services and marketing campaigns that span multiple regions.
- .at domains (Austria) offer another regional lens for testing traffic routing and failover decisions in European networks.
Where to download these lists depends on licensing, data freshness, and whether you need raw domain registrant data or aggregated domain pools. For teams evaluating multi-cloud routing strategies, it’s important to source lists from reputable providers that clearly document usage rights and update frequency. As you explore options, consider how the data will be used in routing decisions and whether you also need enrichment like registration data or RDAP/WHOIS-style details. In the domain-data space, RDAP (Registration Data Access Protocol) offers a modern, machine-readable approach to registration data, with a shift away from legacy WHOIS in many registries. See ICANN’s RDAP resources for implementation details.
For those who want a consolidated data source that aligns with routing workflows, providers such as WebAtla offer curated TLD directories and bulk data resources, including lists by TLD. This can complement your internal data enrichment and routing policies. WebAtla: TLD Directory and WebAtla Pricing provide examples of how domain data products are packaged for enterprise use.
How to obtain and use these lists responsibly
Getting a reliable download of domain lists involves a few guardrails:
- Check licensing and terms of use: Ensure you have rights to use the data for internal testing, analytics, or operational routing. Some providers offer bulk data under commercial licenses that cover redistribution within your own infrastructure.
- Assess freshness and coverage: Frequency of updates matters for routing decisions, stale lists can mislead failover tests or traffic maps. Prefer sources with clear update cadence and change logs.
- Enrichment and validation: Pair the raw domain list with enrichment (RDAP-based registration data, registrar information) to reduce false positives and improve routing decisions. See ICANN’s RDAP resources for implementation guidance. RDAP overview
- Consider data hygiene: Normalize domain formats, deduplicate, and classify by region, intent, or risk profile before plugging into routing rules.
- Respect privacy and legal constraints: Be mindful of regional data-protection rules and the implications of using bulk domain data in commercial products or automated processes.
When applying these lists to a real-world routing scenario, you’ll often pair them with resilience patterns such as DNS failover, latency-based routing, and anycast-style edge distribution. For example, DNS failover often benefits from explicit health checks and quick TTLs to reduce convergence time during outages. See AWS’ guidance on configuring DNS failover and latency-based routing as a practical baseline. DNS failover configuration and DNS best practices for Route 53.
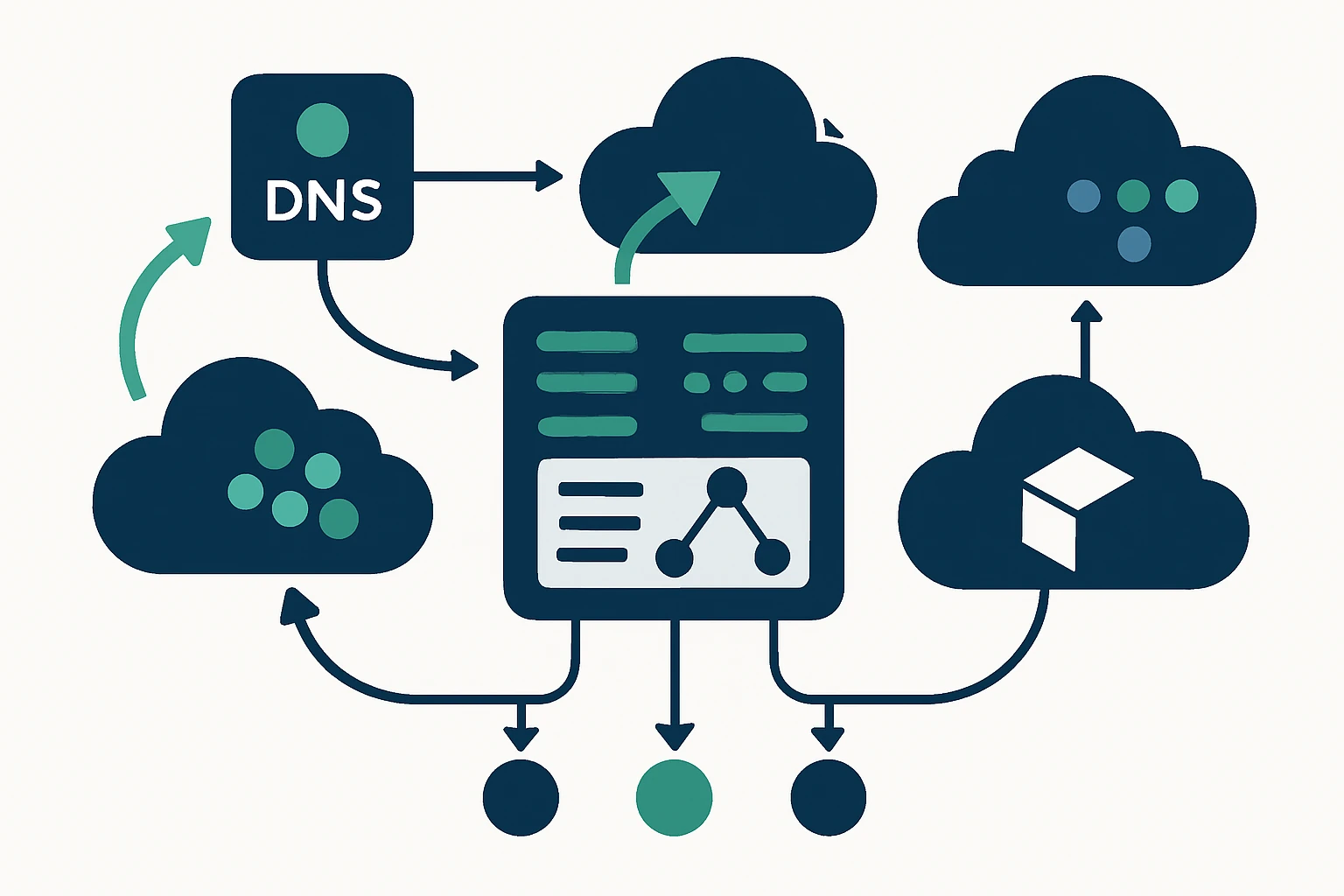
Practical workflows: integrating domain lists into cloud routing and traffic engineering
Integrating domain lists into routing workflows begins with a disciplined data-operations approach. Below is a practical example aligned with common enterprise needs:
- Discovery and inventory: Compile domain lists by TLD and tag them by region or business unit.
- Validation and enrichment: Validate domain formats and enrich with RDAP-like data to understand ownership and registration details.
- Routing strategy alignment: Map domain footprints to edge locations, then align with latency targets and cost considerations.
- Failover test planning: Run controlled failover tests to verify DNS health checks and regional rerouting using representative domains from the lists.
In this context, a structured framework helps operators turn bulk domain data into actionable routing rules without overspecifying infrastructure. A compact framework you can adopt is described in the next section as a four-step process, implemented as a lightweight set of checks within your deployment pipelines.
Domain List Utilization Framework (a practical four-step approach)
- 1. Inventory surface area - Gather domain lists by TLD and classify endpoints by purpose (marketing, partner integrations, external APIs). This establishes the scope for routing considerations.
- 2. Validate and enrich - Normalize formats and attach enrichment (registrar, RDAP-like data) to reduce ambiguity and improve decision-making in routing rules.
- 3. Segment by purpose - Separate lists into cohorts (risk monitoring, performance testing, brand protection) so that routing policies can be tuned per-use case.
- 4. Integrate into routing policies - Feed validated lists into DNS failover configurations, anycast edge routing decisions, and BGP-based path selection where appropriate.
Implementing this framework helps teams avoid common pitfalls, such as treating bulk lists as monolithic inputs or failing to refresh data in line with incident response cycles. When used thoughtfully, domain lists become a governance layer for routing decisions rather than a pure data dump.
Limitations and common mistakes
- Relying on outdated lists: Domain ecosystems change rapidly, stale data can cause failed failovers or misdirected traffic.
- Inadequate licensing: Bulk-domain data often comes with usage restrictions. Ignoring licenses can lead to legal and operational issues.
- Overfitting routing to surface data: Treating lists as the sole driver of routing decisions can introduce brittleness. Always pair with real-time health checks and performance metrics.
- Under-enrichment: Pure lists without registration data or ownership context may misclassify legitimate traffic as risky or vice versa.
Experts emphasize combining domain intelligence with robust routing patterns. For example, modern DNS routing benefits from latency-aware policies and health checks to converge quickly during outages. See AWS Route 53 guidance on latency-based routing and health checks, which illustrate how to design resilient routing that adapts to changing network conditions. DNS failover configuration and Route 53 best practices.
Expert insight
Expert insight from a network architect: "In practice, domain lists should be one input among many in a resilient routing strategy. They help with inventory and testing, but the control plane must remain responsive to real-time health signals and user proximity. The fastest wins come from pairing domain data with latency-aware routing and healthy-endpoint checks, then validating with small, reversible tests before broad rollout."
For teams seeking scalable data and test data pipelines, WebAtla’s TLD directory provides bulk options for cz, me, and at domains, helping teams assemble curated lists aligned with licensing and update cadence. WebAtla: TLD Directory
Conclusion: turning domain lists into resilient cloud routing
Domain lists for cz, me, and at domains offer tangible value when used as structured inputs for DNS failover, latency-aware routing, and multi-cloud traffic engineering. The key is to source reputable data with clear licensing, enrich it with registration context, and weave it into a disciplined routing framework that includes health checks and performance metrics. By combining reliable data with robust routing practices, organizations can reduce latency, improve uptime, and maintain agility across multi-cloud environments. If you’re looking for curated domain data to support these workflows, consider leveraging providers that offer bulk lists and clear licensing while integrating seamlessly with your routing stack. For more on how to access domain data and related pricing, see WebAtla’s TLD directory and pricing pages.
References and further reading
RDAP and Whois context: ICANN Registration Data Access Protocol (RDAP)
DNS failover and latency-based routing: AWS Route 53: DNS failover • Route 53 best practices
Anycast and global routing concepts: Cloudflare: A Brief Anycast Primer