Introduction: a world of latency, outages, and multi-cloud complexity
For SaaS providers, DevOps teams, and enterprises operating across AWS, Google Cloud, and Azure, routing decisions are not just about fast paths - they are existential. Any regional outage, a slow DNS response, or a suboptimal cross‑cloud path can cascade into degraded user experiences, increased support loads, and missed revenue targets. Cloud routing optimization is not a single technology, it is a disciplined practice that blends global routing, DNS health checks, and traffic engineering to minimize latency and maximize uptime. The cloud routing conversation often starts with a simple question: how do we reliably deliver traffic to the healthiest endpoint, wherever it resides? The answer lies in a layered strategy that combines network-layer resilience (BGP), application-facing resilience (DNS failover), and global distribution tactics (anycast). This article outlines a practical framework, grounded in industry practices, to help teams design and operate a resilient multi-cloud routing posture. For domain inventories and live data sources that underpin such planning, see the List of domains by TLD and RDAP & WHOIS Database resources from WebAtla, which provide the data foundation for decision-making in complex, multi-cloud networks.
Why cloud routing optimization matters in multi-cloud ecosystems
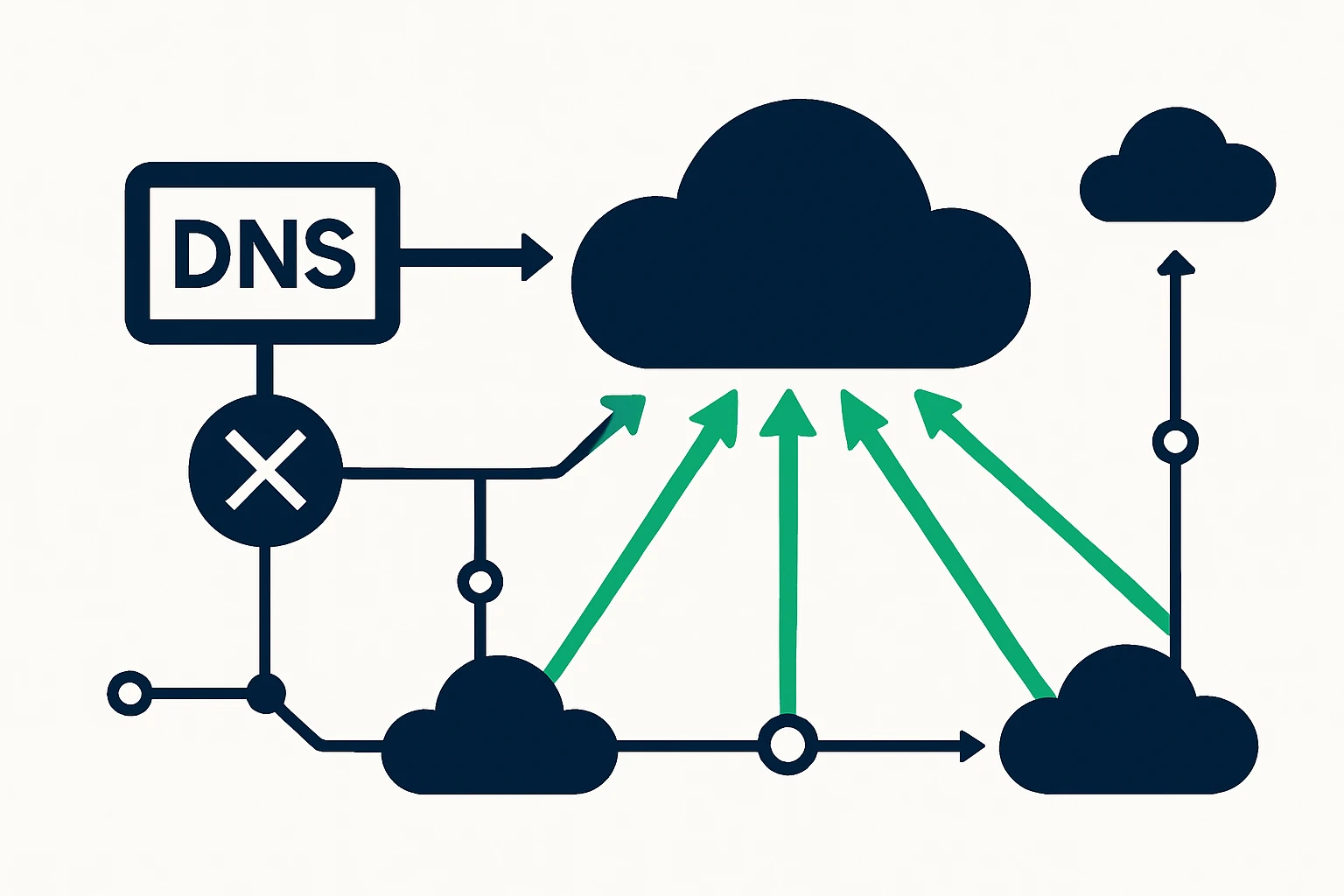
Multi-cloud environments offer flexibility and resilience, but they also fragment control over routing and DNS, which means performance gains are often incremental, not revolutionary. A modern optimization approach blends several layers of control: fast failover at the DNS layer, robust interconnectivity with BGP optimization, and a distribution strategy that reduces reachability latency for end users. Industry best practices increasingly emphasize three pillars: cloud-router reliability, DNS-based resilience, and globally distributed anycast-like behavior to route clients to nearby endpoints.
From a routing perspective, best-practice guidance emphasizes not only how to detect failures but how to respond to them in a way that preserves user experience. For example, cloud providers advise enabling high-availability features such as Bidirectional Forwarding Detection (BFD) and graceful restart in BGP sessions to shorten recovery times after link or router failures. This reduces the window during which traffic might take longer, suboptimal, or entirely fail to reach a destination. Practically, this means co‑deploying BGP optimization with DNS failover so that if a regional path goes down, traffic quickly shifts to a healthy path at either the network or DNS layer. Google Cloud: Best Practices for Cloud Router stresses the importance of BFD and graceful restart for minimizing disruption in cloud interconnects.
DNS resilience is another critical layer. DNS-based failover is a pragmatic complement to network-layer routing: it can redirect clients to healthier endpoints when monitoring detects problems, while TTL management and health checks help ensure timely redirection. TechTarget’s recent overview of DNS optimization highlights balancing DNS failover with performance considerations and the need for continuous health monitoring to maintain service levels. TechTarget: How to optimize DNS for reliable business operations. For external DNS resiliency, the most credible guidance focuses on distributing DNS responses across multiple points of presence to mitigate routing outages. CIRA: Best Practices for Improving External DNS Resiliency.
A practical framework for multi-cloud traffic engineering
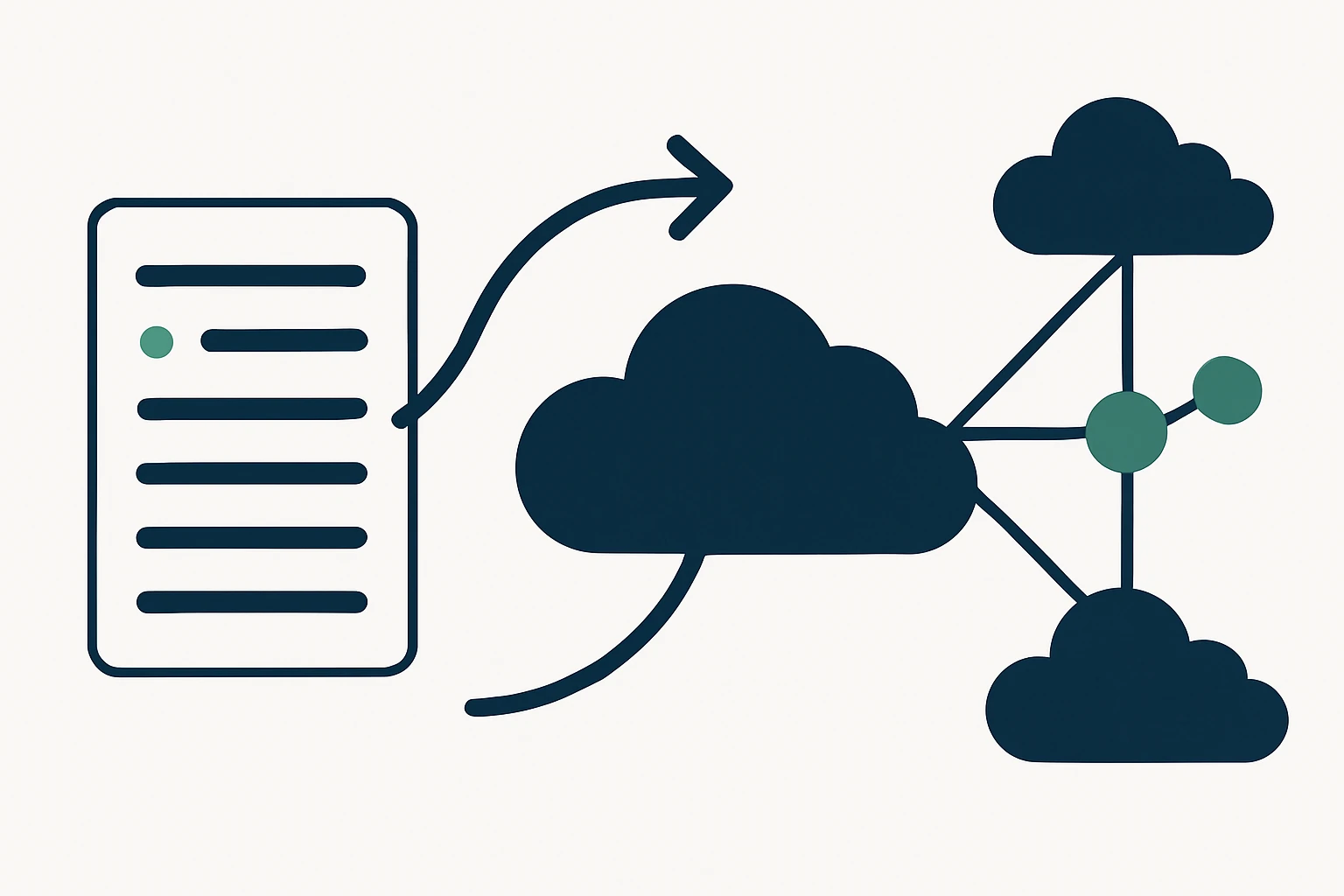
Below is a concise framework designed to help teams reason through a domain inventory, DNS strategy, and routing topology in a multi-cloud setting. The framework is intentionally vendor-agnostic and emphasizes concrete, auditable steps rather than abstract theory.
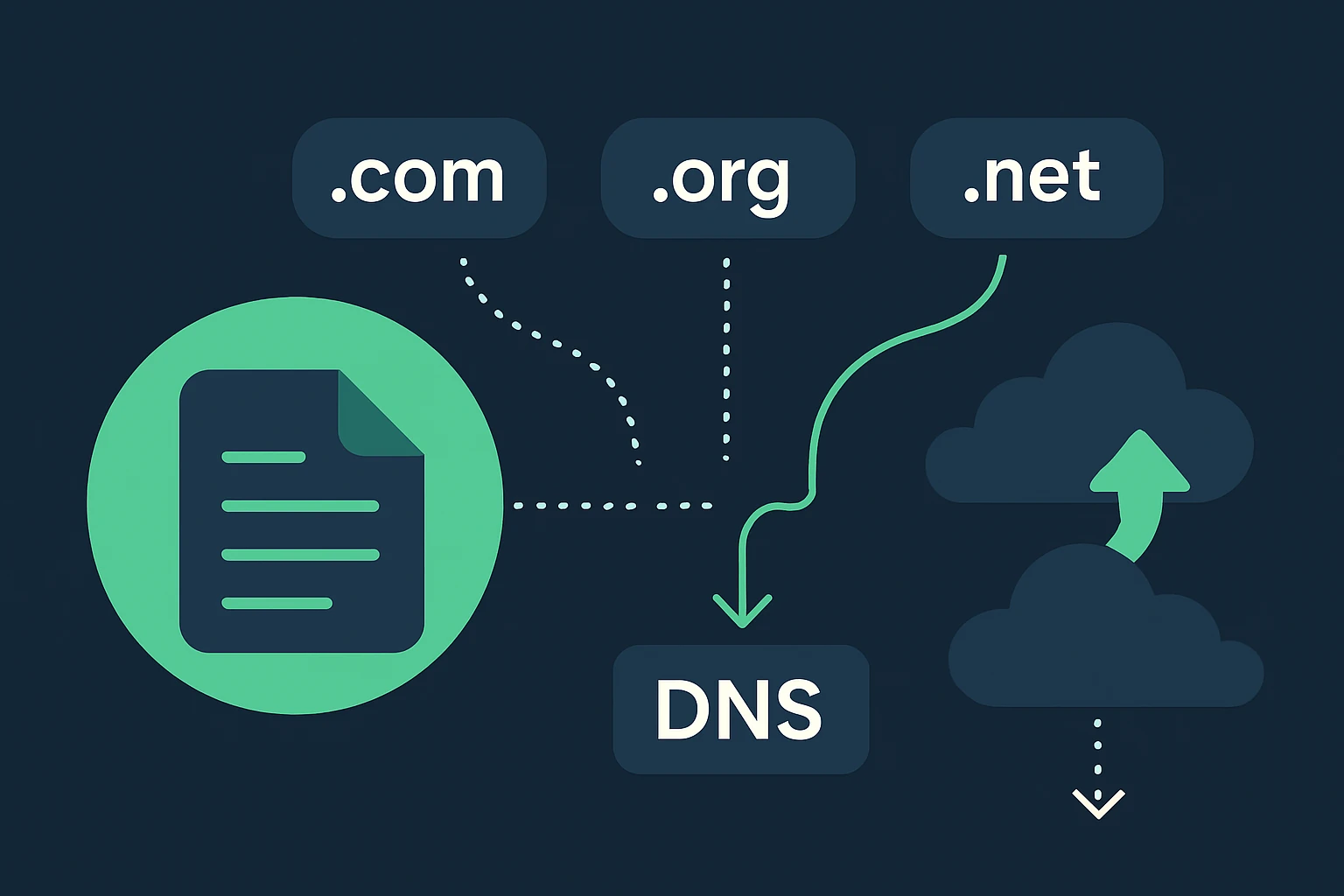
- Step 1 - Build a domain inventory for resilient routing. Start by identifying the domains and TLDs you must support across cloud regions. Leverage authoritative sources to understand which TLDs are most relevant for your user base and regulatory needs. If you rely on a broad inventory for DNS failover planning, the publisher's own catalog of domains by TLD can serve as a starting point, including the List of domains by TLD resource. You may also reference data sets such as the RDAP & WHOIS Database to ensure domain ownership and registration status inform routing decisions.
- Step 2 - Map domains to routing roles (primary vs failover). For each domain or service endpoint, define a primary cloud location and one or more failover targets. This mapping should align with regional latency expectations, regulatory constraints, and the availability of cross‑cloud connectivity (for example, cross-region VPC or VNET peering). A clear mapping helps operations automate failover with both DNS and network routing in tandem.
- Step 3 - Decide on a DNS strategy that complements BGP resilience. Implement DNS health checks and thoughtful TTL values that balance fast failover with DNS query load. DNS failover should act as a safety valve that complements, not replaces, network-layer redundancy. Look to DNS optimization best practices for guidance on health checks, TTL tuning, and minimizing negative impact from DNS caching. TechTarget: How to optimize DNS for reliable business operations.
- Step 4 - Implement BGP optimization in concert with DNS failover. Use BGP features to improve convergence times and path selection across cloud regions, while DNS failover handles endpoint redirection when a path becomes unhealthy. Google Cloud’s guidance on Cloud Router emphasizes enabling BFD and graceful restart to reduce disruption during routing changes. Google Cloud: Best Practices for Cloud Router.
- Step 5 - Embrace anycast-like distribution for latency reduction. While true global anycast requires infrastructure collaboration, many organizations emulate the effect by routing clients to the nearest healthy endpoint through distributed DNS and multi‑site deployments. This approach contributes to reduced latency and resilient user experiences in geographies loaded by diverse cloud locations. For a detailed explanation of anycast concepts and their practical impact, refer to industry analyses and practitioner guides (the concept is widely adopted in large-scale DNS and CDN deployments).
- Step 6 - Instrumentation and proactive monitoring. Track latency, DNS resolution times, failover frequency, and the time-to-detect (TTD) and time-to-recover (TTR) metrics. Transparent dashboards across DNS health checks, BGP session status, and inter-cloud latency help you validate whether your routing posture meets service‑level expectations.
- Step 7 - Security and governance considerations. Ensure DNSSEC where appropriate, monitor for BGP anomalies, and implement access controls for routing configuration changes. The combination of DNS resilience and secure interconnects mitigates a broad class of outages.
- Step 8 - Testing, validation, and continuous improvement. Periodically simulate outages and perform disaster recovery drills to validate both DNS failover and BGP-based routing changes. Realistic drills reveal timing gaps, misconfigurations, and potential data-plane disruptions that are not obvious during normal operation.
In practice, this framework supports a holistic approach to cloud routing optimization across multi-cloud environments. It harmonizes services, networks, and DNS so that latency is minimized and uptime is maximized, even in the face of complex failures. For teams building domain inventories, WebAtla’s TLD‑level catalog and RDAP/WHOIS data can be valuable inputs to ensure the routing posture is grounded in real ownership and configuration details.
Limitations and common mistakes to avoid
While the combined use of DNS failover, BGP optimization, and anycast-inspired distribution can significantly improve reliability and performance, there are notable caveats and pitfalls to watch for.
- DNS failover is not instantaneous. DNS changes propagate with TTLs and caching, which means failover may not be immediate even with frequent health checks. Align expectations with a layered approach where DNS acts as a safety valve alongside rapid network failover.
- TTL tuning trade-offs. Very low TTLs can increase resolution load and DNS query volume, while higher TTLs slow down failover. Strike a balance based on your service level objectives and traffic patterns.
- BGP misconfigurations risk outages. Incorrect BGP announcements or filters can cause traffic black-holes or inadvertent congestion. Regular configuration validation and change control reduce these risks.
- Anycast complexity and visibility. True global anycast requires coordinated routing policies and infrastructure, emulations must be implemented with care to avoid suboptimal routing in some regions.
- Security implications of DNS and routing changes. Continuous monitoring for DNS amplification, route leaks, and hijacks is essential when deploying dynamic failover strategies.
Structured approach recap: a compact framework you can apply
- Inventory domains by TLDs as your data foundation. Use an organized list (e.g., the publisher’s TLD catalog) to identify the surface area for routing, ensuring you capture critical domains across the geographies you serve.
- Define routing roles for each domain (primary, secondary, backup) to align with latency targets and regional availability.
- Choose a DNS strategy that complements network resilience with health checks and pragmatic TTLs.
- Implement BGP optimization for inter-cloud paths including graceful restart if supported by your infrastructure.
- Incorporate anycast-inspired distribution to shorten effective distance and improve perceived latency for end users.
- Monitor, test, and iterate on latency, reachability, and failover performance to drive continuous improvement.
- Guardrails and security to protect DNS and routing configuration from misconfigurations or attacks.
Conclusion: a disciplined path to lower latency and higher uptime
Cloud routing optimization in multi-cloud environments is not a single trick but a disciplined, layered approach. By combining DNS-based failover with network-layer reliability and a domain inventory-driven workflow, teams can shorten failover times, reduce end-user latency, and maintain higher service availability. The practical framework outlined here invites teams to start with a domain inventory, articulate clear routing roles, and then align DNS, BGP, and anycast-like strategies into a cohesive operational model. As cloud networks continue to grow in breadth and complexity, this integrated approach helps ensure the right traffic paths are chosen at the right times - consistently and transparently for users. For readers seeking direct data inputs to underpin such decisions, the WebAtla catalog and RDAP/WHOIS data provide accessible references to domain ownership and registration status to support governance and compliance in routing decisions.
Notes & references: for DNS health optimization and resilience frameworks, see TechTarget, CIRA, and Google Cloud.
Related resources from the client include List of domains by TLD and RDAP & WHOIS Database for domain-level visibility and registration information, supporting data-driven routing decisions in complex, multi-cloud networks.