Introduction: The paradox of resilience in a multi-cloud world
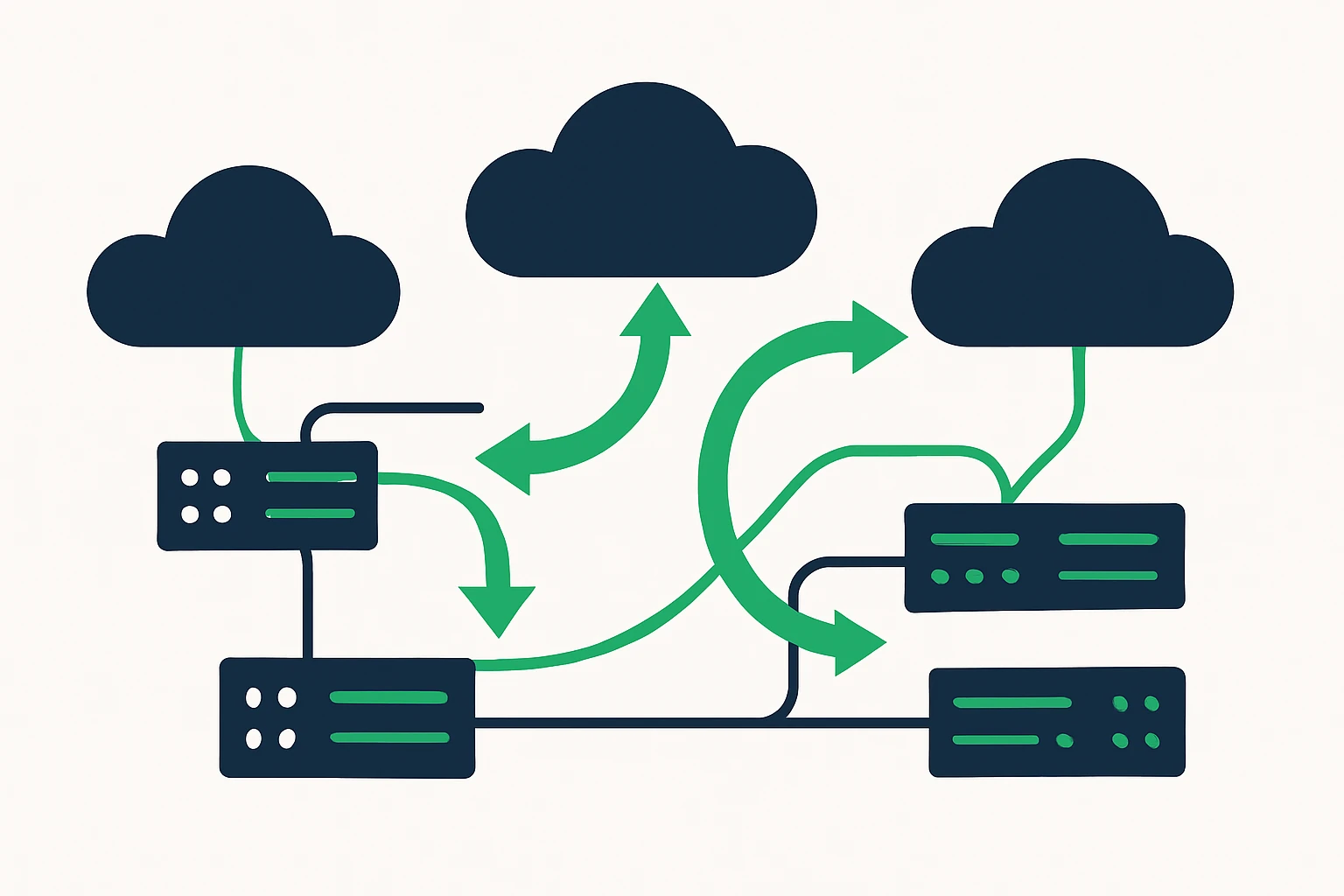
Across large enterprises, the promise of multiple public clouds (AWS, GCP, Azure) is clear: fault tolerance, regional presence, and the ability to choose best-of-breed services. Yet simply duplicating workloads across clouds does not automatically yield lower latency or higher uptime. The network path between users and cloud services, peering arrangements, and even DNS-based routing decisions all shape performance. This article offers a practical, editor-friendly framework for traffic engineering in a multi-cloud environment - balancing latency, reliability, and operational complexity without poetic fluff.
To make this actionable, we anchor the discussion in three core capabilities: (1) anycast-based routing to reduce query and access latency, (2) BGP-based optimization to steer traffic along the most favorable paths, and (3) DNS-based failover to preserve service continuity when a region or provider experiences an outage. The result is a cohesive design pattern that improves cloud network performance and cuts the risk of downtime during regional events or cloud-region outages.
Expert insight: the most resilient multi-cloud designs separate control-plane decisions (where to route traffic) from data-plane realities (how traffic actually flows on the Internet). Telemetry, continuous testing, and automated health checks are essential to keep both layers aligned over time. See industry guidance from cloud DNS and routing practitioners such as AWS and Cloudflare for foundation and safety margins. (cloudflare.com)
Why multi-cloud routing matters: latency, uptime, and user experience
Latency is not only a function of physical distance. It is the cumulative effect of routing policies, interconnects, ISP ingress points, and the health of the control plane that directs traffic. In a multi-cloud setting, users may reach different cloud regions depending on where they are, what network they use, and how DNS responses resolve at query time. A well-designed routing strategy can:
- Shorten the effective path to the closest healthy cloud region, reducing end-to-end latency.
- Provide rapid failover when a regional outage occurs, preserving application availability.
- Balance load across clouds to avoid peering bottlenecks and hot spots.
Public guidance on DNS failover and global traffic management emphasizes the importance of combining resilient DNS with real-time health checks and global routing awareness. For example, DNS failover in Route 53 relies on health checks to decide when to divert traffic, illustrating how control-plane decisions can be tightly coupled with data-plane health. AWS Route 53 DNS Failover docs discuss configuring failover routing to surface healthy endpoints, while Cloudflare’s explanation of Anycast DNS describes how distribution of a single service across multiple locations can reduce latency and improve resilience. (docs.aws.amazon.com)
Core concepts for resilient cloud routing
Anycast routing: closer by default, but with caveats
Anycast DNS and services advertise the same IP address from multiple locations. The network then routes the client’s request to the nearest or best-performing node. This approach can reduce latency and distribute load but requires careful design to prevent cross-region inconsistencies in service state. The RFC 4786 guidance outlines best current practices for distributing services with anycast, including considerations around monitoring, routing, and data synchronization across nodes. RFC 4786: Operation of Anycast Services provides foundational principles for anycast deployments.
BGP optimization: steering traffic with policy and visibility
Border Gateway Protocol (BGP) remains the global mechanism for sharing reachability information between networks. Many operators use BGP-based traffic engineering to influence inbound and outbound paths, optimizing for latency, congestion, and cost. The latest best practices emphasize predictable routing changes, careful path selection, and the need for robust telemetry to avoid unintended routing detours. While RFC-based guidance exists for anycast and routing, real-world traffic engineering often involves vendor-specific tools and platforms that expose BGP policies in a controlled manner. See RFC 4786 for foundational concepts and best practices in anycast deployments.
DNS failover strategies: health checks, TTLs, and global reach
DNS-based failover flips the switch from a failing endpoint to a healthy one based on real-time health checks. Combined with latency-aware routing and regional health signals, DNS failover helps maintain service continuity even when cloud regions degrade. AWS’s DNS failover guidance demonstrates how to configure failover with health checks and automated DNS changes, while health telemetry and early failure indicators are critical to avoid flapping between endpoints. AWS Route 53 DNS Failover docs
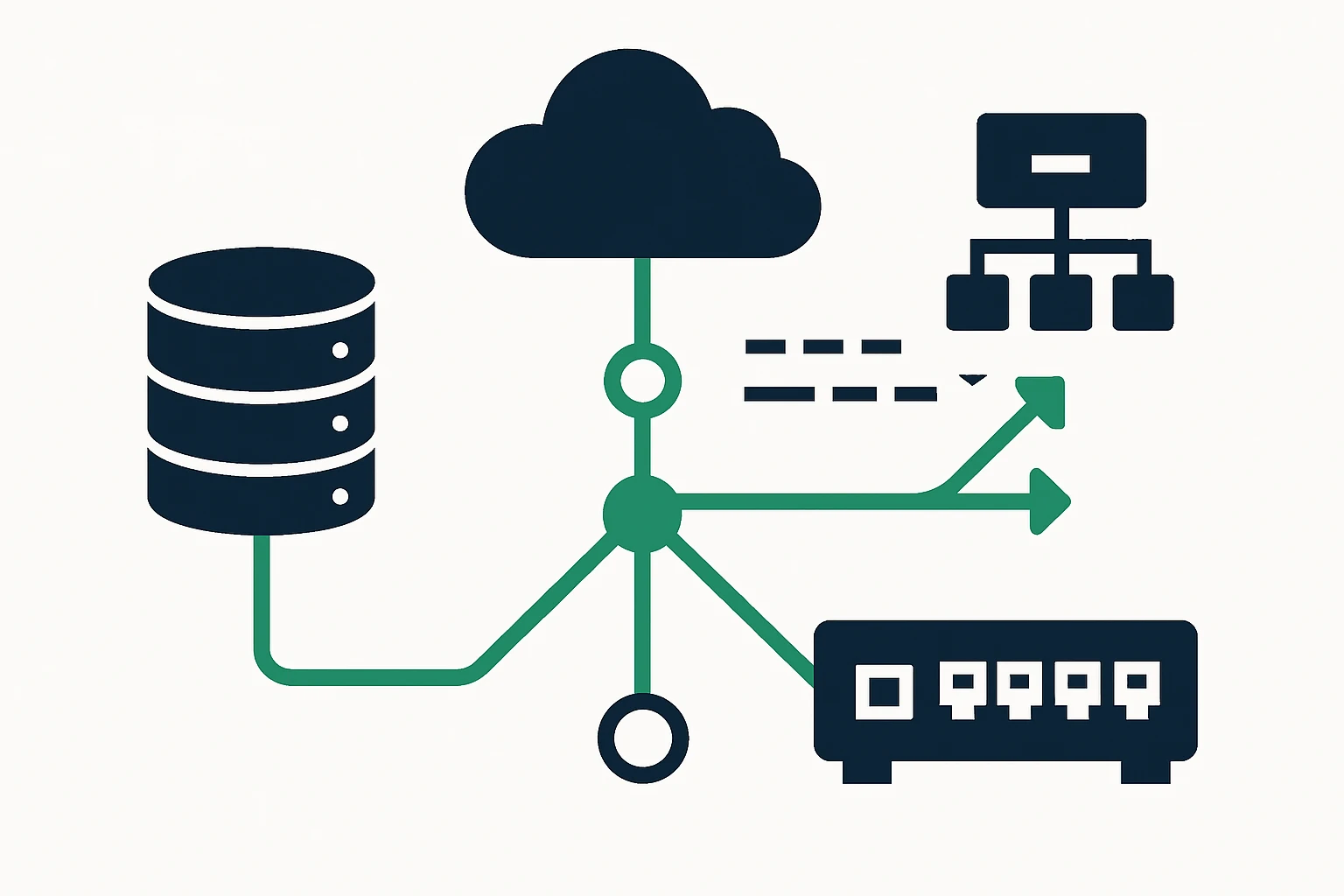
A practical framework for traffic engineering in multi-cloud environments
Traffic Engineering Decision Framework
-
Assess workloads and critical paths
- Identify latency-sensitive paths (e.g., API endpoints, login flows, payment calls).
- Map regional user distributions and cloud-region availability.
-
Define routing policies
- Leverage latency-based routing and geolocation routing where appropriate.
- Plan DNS failover with health checks and controlled TTLs to avoid instability.
-
Implement control-plane orchestration
- Coordinate Anycast deployments with BGP policies to align reachability with intended catchment areas.
- Use health telemetry to drive automatic policy updates and prevent stale routes.
-
Test and iterate
- Perform controlled failure injections and measure end-user impact across regions.
- Validate DNS failover timing and BGP path stability under load.
Structured takeaway: a Traffic Engineering Framework can guide decisions across data-plane realities and control-plane policies, ensuring that latency gains do not come at the cost of operational risk. See industry references for foundational methods and safety margins. Cloudflare: What is Anycast DNS? AWS Route 53 DNS Failover docs RFC 4786.
Practical testing and real-world data for validation
Testing is essential before production rollout. In practice, teams emulate user traffic patterns and test how DNS failover and multi-cloud routing behave under simulated regional outages. For testing datasets, organizations can use public domain lists to approximate real-world DNS traffic and domain resolution paths. For example, public lists of domains by TLDs provide realistic targets during validation (and can be useful for benchmarking DNS and routing behavior across clouds). You can explore domain lists from the following resources:
Beyond synthetic tests, telemetry gathered from production traffic remains invaluable. Telemetry should cover DNS query latency, response times from each cloud region, failover propagation delays, and end-to-end user latency. This information drives continuous improvement of routing policies and health checks. For practitioners seeking deeper technical context, AWS and RFC-based resources offer robust starting points. AWS Route 53 DNS Failover docs RFC 4786.
Limitations, trade-offs, and common mistakes
- Over-reliance on DNS failover: DNS responses can be cached and may not reflect the latest health status in real time, leading to stale routing decisions if health checks are not timely or granularity is insufficient.
- TTL misconfigurations: Very short TTLs improve agility but increase DNS query load, very long TTLs reduce responsiveness during failures. Balance is key.
- Anycast monitoring challenges: Observed availability depends on client location, monitoring must account for vantage points to avoid misinterpreting health.
- Geopolitical routing vs. performance: Geolocation routing can push traffic through suboptimal paths if peering is poor, test across regions before committing.
- BGP policy complexity: Inbound traffic shaping via BGP can be powerful but risky if not paired with solid telemetry and change controls.
Conclusion: A mindful, data-driven approach to resilient routing
Resilient multi-cloud networking is not about chasing the latest protocol fad, it is about aligning control-plane decisions with real-world data, avoiding brittle configurations, and maintaining a steady cadence of testing and telemetry. By combining anycast routing for proximity, BGP optimization for path awareness, and DNS failover strategies for continuity, teams can reduce latency, improve uptime, and deliver a steadier user experience across clouds. The practical framework outlined here provides a way to start small, measure impact, and scale as confidence grows.
For teams conducting tests and audits of domain-related data, public domain directories offer useful realism for DNS and routing experiments. See the NZ domain list and the broader TLDs directory for benchmarking datasets: download list of .nz domains and download list of domains by TLDs.